Configuring AWS CloudTrail Connectors
This connector allows Stellar Cyber to collect data from external sources and add the records to the data lake. The incoming information is included in Interflow records in the AWS Events index.
Integration with AWS and S3 enables organizations to securely store and manage their data while providing real-time threat detection and response capabilities through Stellar Cyber's advanced security analytics and machine learning algorithms.
You can have any number of AWS connectors active in the system. You will typically have one or two connectors for each account being used by anyone in the network.
However, if you have AWS Control Tower set up, you can use an asterisk as a wildcard character instead of a specific Account ID in the Prefix field.![]()
Stellar Cyber connectors with the Collect function (collectors) may skip collecting some data when the ingestion volume is large, which potentially can lead to data loss. This can happen when the processing capacity of the collector is exceeded.
Connector Overview: AWS CloudTrail
Capabilities
-
Collect: Yes
-
Respond: No
-
Native Alerts Mapped: No
-
Runs on: DP
-
Interval: 5 minutes
Collected Data
|
Content Type |
Index |
Locating Records |
|---|---|---|
|
cloudtrail vpcflow waf |
AWS Events (non-traffic) Traffic (VPC flow) |
Domain
|
https://s3.amazonaws.com https://s3-<Region>.amazonaws.com https://<Bucket>.s3.amazonaws.com |
Response Actions
N/A
Third Party Native Alert Integration Details
N/A
Required Credentials
-
Bucket, Prefix, Access Key ID, and Secret Access Key
Let us know if you find the above overview useful.
Adding an AWS CloudTrail Connector
To add an AWS CloudTrail connector:
- Create an AWS CloudTrail trail
- Add a user with the appropriate permissions
- Create an access key
- Get the required information
- Add the connector in Stellar Cyber
- Test the connector
- Verify ingestion
Creating the AWS CloudTrail Trail
To create an AWS CloudTrail trail:
Use our example as a guideline, as you might be using a different software version.
-
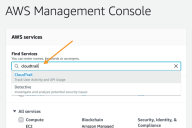
Log in to your AWS Management Console at https://aws.amazon.com .
-
In Find Services, start entering cloudtrail. As you type, suggestions appear. Click on CloudTrail.
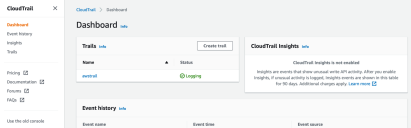
The CloudTrail Dashboard appears.
-
Click Create trail. The Choose trail attributes page appears.
- Enter a Trail name.
- Leave the default configurations for the various event information settings.
- Under Storage location, choose Yes for Create a new S3 bucket.
-
Enter the name.
Make note of this, as you need the bucket name when configuring the connector in Stellar Cyber.
- Enter the AWS KMS alias.
- Leave the remaining options at the default settings.
-
Click Next. The Choose log events page appears.
- Choose the events you want to send to Stellar Cyber. We recommend choosing all of them.
- Click Next. The Review and create page appears.
- Click Create trail. The trail is added, and displayed on the Trails page.
Adding a User with the Appropriate Permissions

To add a user with the appropriate permissions:
-
Log in to your AWS Management Console at https://aws.amazon.com/console. View the services in the Console Home or choose View all services.
-
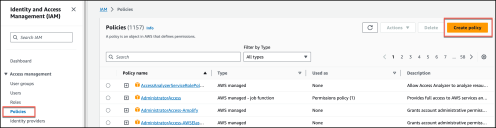
Choose IAM. The IAM Dashboard appears.
-
Choose Policies and then choose Create Policy.
-
In the Create policy pane, choose the JSON tab.
-
Using the example below as a guide, edit the JSON policy document.
The following is just an EXAMPLE. You must modify this JSON to match the resources in your own environment.
CopyCloudTrail policy{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "VisualEditor0",
"Effect": "Allow",
"Action": [
"s3:GetObject",
"s3:ListBucket"
],
"Resource": [
"arn:aws:s3:::<bucket_name>",
"arn:aws:s3:::<bucket_name>/*",
}
]
}
For example:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "VisualEditor0",
"Effect": "Allow",
"Action": [
"s3:GetObject",
"s3:ListBucket"
],
"Resource": [
"arn:aws:s3:::stellarcybercloudtrail",
"arn:aws:s3:::stellarcybercloudtrail/*"
]
}
]
} -
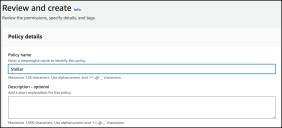
Choose Next.
-
Give your policy a name to associate it with Stellar Cyber, then choose Create policy.
The policy can now be attached to a user.
-
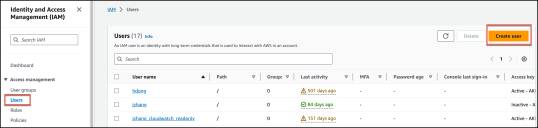
From the IAM navigation pane, choose Users and then choose Create user.
-
In the Specify user details page for User details, enter a User name for the new user.
-
Choose Provide user access to the – AWS Management Console optional to produce login credentials for the new user, such as a password.
-
Choose how you want to create the Console password and then choose Next.
-
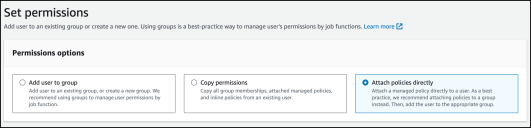
For Set permissions, choose Attach policies directly. Then search for the policy you created above.
-
Select the checkbox to the left of the policy name, then choose Next.
-
Verify the information and then choose Create user.
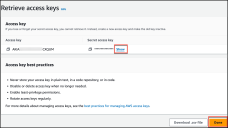
Creating an Access Key
-
Log in to the IAM Console with your AWS account ID, your IAM user name, and password. You must have the permissions required to create access keys for a user.
-
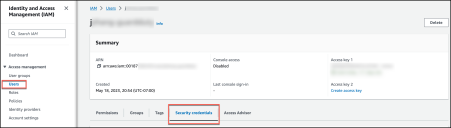
Choose Users, then choose the user name, and click Security credentials.
-
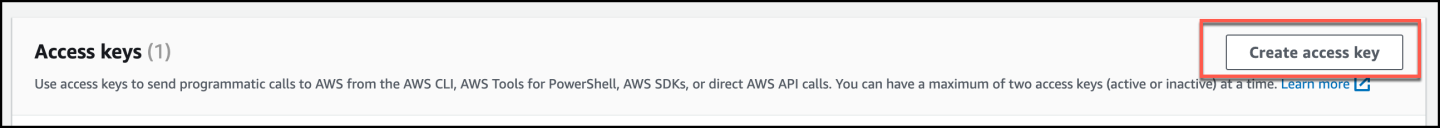
In the Access keys section, choose Create access key. Access keys have two parts: an access key ID and a secret access key. Click Create access key.
-
On the Access key best practices & alternatives page, choose Other and then choose Next.
-
Click Create access key.
-
On the Retrieve access keys page, choose Show to reveal the value of the user's secret access key. Save the access key ID and secret access key in a secure location. You will need them when configuring the connector in Stellar Cyber.
-
Click Done.
Getting the Required Information
To add the connector in Stellar Cyber you need the following:
- Bucket (you copied this earlier)
- Prefix
- Access key ID (you copied this earlier)
- Secret access key (you copied this earlier)
To get the prefix:
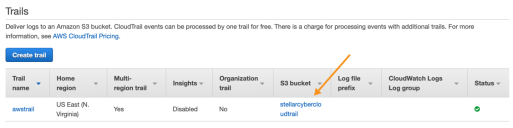
- In the CloudTrail Dashboard, click Trails. The existing trails appear.
-
For the trail you are using, the Bucket is the name in the S3 bucket column.
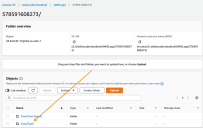
- Click the bucket name. The bucket info appears.
-
Click the CloudTrail object.
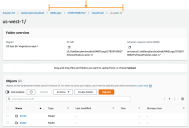
The regional objects appear.
-
Click your region. The Prefix is the path at the top of the screen, starting with AWSLogs (the default) and ending with the region.
In our example the path is AWSLogs/578591608273/CloudTrail/us-west-1/. Copy your path. This is what you paste into the Prefix field in Stellar Cyber.
If you're configuring an AWS WAF connector and you have a custom prefix , use your custom prefix. If you are using a date in your custom prefix, you must replace static numbers with variables, converting the prefix to a pattern that Stellar Cyber can recognize. Following are the variables.
Variable Definition //YYYY// 4 digit year //m// 1 or 2 digit month //mm// 2 digit month //d// 1 or 2 digit day //dd// 2 digit day //H// 1 or 2 digit hour //HH// 2 digit hour //M// 1 or 2 digit minute //MM// 2 digit minute For example, CustomPrefix/year=/2020/month=/10/day=/27/ becomes CustomPrefix/year=///YYYY///month=///mm///day=///dd//.
For the CloudTrail connector, the supported prefix syntax may also include Organization ID, as shown here:
-
Without Organization ID:
optional_prefix_name/AWSLogs/Account ID/CloudTrail/region -
With Organization ID:
optional_prefix_name/AWSLogs/OU-ID/Account ID/CloudTrail/region
Adding the Connector in Stellar Cyber
With the trail set up and the bucket name and path handy, you can add the AWS CloudTrail connector in Stellar Cyber:
-
Log in to Stellar Cyber.
-
Click System | Integration | Connectors. The Connector Overview appears.
-
Click Create. The General tab of the Add Connector screen appears. The information on this tab cannot be changed after you add the connector.
The asterisk (*) indicates a required field.
-
Choose PaaS from the Category drop-down.
-
Choose AWS CloudTrail from the Type drop-down.
-
For this connector, the supported Function is Collect, which is enabled already.
-
Enter a Name.
This field does not accept multibyte characters.
-
Choose a Tenant Name. The Interflow records created by this connector include this tenant name.
-
Choose the device on which to run the connector.
-
(Optional) When the Function is Collect, you can create Log Filters. For information, see Managing Log Filters.

-
Click Next. The Configuration tab appears.
The asterisk (*) indicates a required field.
-
Choose a Sub Type.
-
cloudtrail—feeds account activity information, including actions taken through the AWS Management Console and various AWS SDKs and command line tools. See the AWS CloudTrail documentation for details.
-
vpcflow—provides network-level information. See the AWS VPC documentation for details.
-
waf—provides Web Application Firewall information. See the AWS WAF documentation for details.
-
-
Enter the Proxy URI, if you have one.
-
Enter the Bucket you noted earlier.
-
Enter the Prefix you noted earlier. The supported prefix syntax is as follows:
-
Without Organization ID:
optional_prefix_name/AWSLogs/Account ID/CloudTrail/region -
With Organization ID:
optional_prefix_name/AWSLogs/OU-ID/Account ID/CloudTrail/region
-
-
With Organization ID and AWS Control Tower:
optional_prefix_name/AWSLogs/OU-ID/*/CloudTrail/region
The Sub Type must be cloudtrail or vpcflow.
-
Enter the Access Key ID from IAM.
-
Enter the Secret Access Key from IAM.
-
Enter the File Type. The cloudtrail and vpcflow sub types should always be gzip. The waf sub type can be gzip or text.
-
(Optional) Choose a Region from the available regions in the drop-down.
-
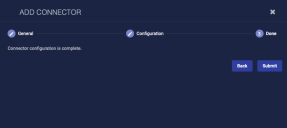
Click Next. The final confirmation tab appears.
-
Click Submit.
To pull data, a connector must be added to a Data Analyzer profile if it is running on the Data Processor.
The new connector is immediately active and starts collecting logs.
Testing the Connector
If you have AWS Control Tower, the Test button tests all account IDs.![]()
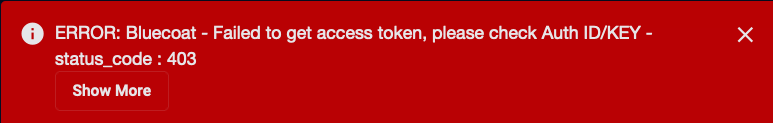
When you add (or edit) a connector, we recommend that you run a test to validate the connectivity parameters you entered. (The test validates only the authentication / connectivity; it does not validate data flow).
For connectors running on a sensor, Stellar Cyber recommends that you allow 30-60 seconds for new or modified configuration details to be propagated to the sensor before performing a test.
-
Click System | Integrations | Connectors. The Connector Overview appears.
-
Locate the connector that you added, or modified, or that you want to test.
-
Click Test at the right side of that row. The test runs immediately.
Note that you may run only one test at a time.
Stellar Cyber conducts a basic connectivity test for the connector and reports a success or failure result. A successful test indicates that you entered all of the connector information correctly.
To aid troubleshooting your connector, the dialog remains open until you explicitly close it by using the X button. If the test fails, you can select the button from the same row to review and correct issues.
The connector status is updated every five (5) minutes. A successful test clears the connector status, but if issues persist, the status reverts to failed after a minute.
Repeat the test as needed.
Verifying Ingestion
To verify ingestion:
- Click Investigate | Threat Hunting. The Interflow Search tab appears.
- Change the Indices to include either or both of AWS Events or Traffic. The table immediately updates to show ingested Interflow records.