Configuring Proofpoint on Demand Connectors
Use this Stellar Cyber connector to ingest Proofpoint on Demand email logs to the data lake. This connector uses Proofpoint's streaming API. It keeps an open WebSocket connection to get streaming data.
The following license is required: Proofpoint On Demand’s Remote Syslog.
If your Stellar Cyber deployment is configured to use an HTTP proxy, be advised that this connector relies on Proofpoint’s API, which uses the WebSocket protocol for log collection (WebSocket is not reliable over HTTP proxy connections).
Stellar Cyber connectors with the Collect function (collectors) may skip collecting some data when the ingestion volume is large, which potentially can lead to data loss. This can happen when the processing capacity of the collector is exceeded.
Connector Overview: Proofpoint on Demand
Capabilities
-
Collect: Yes
-
Respond: No
-
Native Alerts Mapped: No
-
Runs on: DP
-
Interval: Every hour
Collected Data
|
Content Type |
Index |
Locating Records |
|---|---|---|
|
Mail Log Message |
Syslog |
Domain
|
logstream.proofpoint.com:443 |
Response Actions
N/A
Third Party Native Alert Integration Details
N/A
Required Credentials
-
Cluster ID and API Key
Let us know if you find the above overview useful.
Adding a Proofpoint on Demand Connector
To add a Proofpoint on Demand connector:
Obtaining Prerequisites
If your Stellar Cyber deployment is configured to use an HTTP proxy, be advised that this connector relies on Proofpoint’s API, which uses the WebSocket protocol for log collection (WebSocket is not reliable over HTTP proxy connections).
Before you configure the connector in Stellar Cyber, you must obtain and verify the following from your POD deployment.
-
Configuration of this connector requires your Proofpoint deployment be licensed for Proofpoint On Demand’s Remote Syslog.
-
-
To configure collection of maillog and message together in one connector : One API key is needed.
-
To configure collection of maillog or message in two separate connectors: The same API key can be used for the two connectors.
-
To configure collection of maillog in more than one connector: You need a different API key for each connector.
-
To configure collection of message in more than one connector: You need a different API key for each connector.
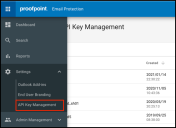
Generate API keys from the Admin portal at https://admin.proofpoint.com. Choose API Key Management under Settings.
-
-
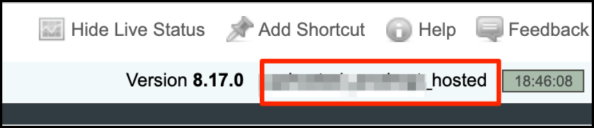
Cluster ID This is assigned by Proofpoint and is located at the top of the Proofpoint on Demand deployment management interface.
Adding the Connector in Stellar Cyber
To add a Proofpoint on Demand connector in Stellar Cyber:
-
Log in to Stellar Cyber.
-
Click System | Integration | Connectors. The Connector Overview appears.
-
Click Create. The General tab of the Add Connector screen appears. The information on this tab cannot be changed after you add the connector.
The asterisk (*) indicates a required field.
-
Choose Email from the Category drop-down.
-
Choose Proofpoint on Demand from the Type drop-down.
-
For this connector, the supported Function is Collect, which is enabled already.
-
Enter a Name.
Notes:- This field does not accept multibyte characters.
- It is recommended that you follow a naming convention such as tenantname-connectortype.
-
Choose a Tenant Name. The Interflow records created by this connector include this tenant name.
-
Choose the device on which to run the connector.
-
(Optional) When the Function is Collect, you can apply Log Filters. For information, see Managing Log Filters.

-
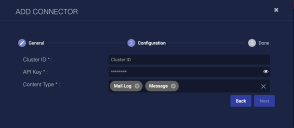
Click Next. The Configuration tab appears.
The asterisk (*) indicates a required field.
-
Enter the Cluster ID you obtained earlier.
-
Enter the API Key you obtained earlier.
-
Choose the Content Type you would like to collect. The logs for Mail Log and Message are supported.
-
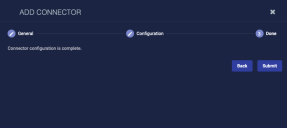
Click Next. The final confirmation tab appears.
-
Click Submit.
The new connector is immediately active.
A new Proofpoint on Demand connector automatically collects logs for the last 7 days. It can take a few days for the logs to be current.
Testing the Connector
When you add (or edit) a connector, we recommend that you run a test to validate the connectivity parameters you entered. (The test validates only the authentication / connectivity; it does not validate data flow).
For connectors running on a sensor, Stellar Cyber recommends that you allow 30-60 seconds for new or modified configuration details to be propagated to the sensor before performing a test.
-
Click System | Integrations | Connectors. The Connector Overview appears.
-
Locate the connector that you added, or modified, or that you want to test.
-
Click Test at the right side of that row. The test runs immediately.
Note that you may run only one test at a time.
Stellar Cyber conducts a basic connectivity test for the connector and reports a success or failure result. A successful test indicates that you entered all of the connector information correctly.
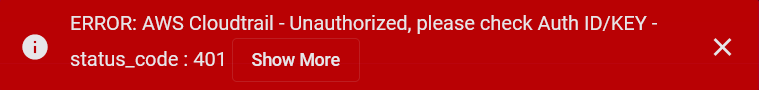
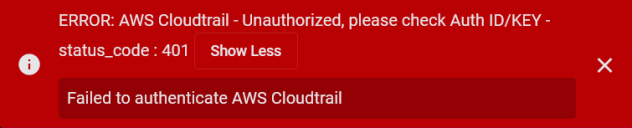
To aid troubleshooting your connector, the dialog remains open until you explicitly close it by using the X button. If the test fails, you can select the button from the same row to review and correct issues.
The connector status is updated every five (5) minutes. A successful test clears the connector status, but if issues persist, the status reverts to failed after a minute.
Repeat the test as needed.
If the test fails, the common HTTP status error codes are as follows:
| HTTP Error Code | HTTP Standard Error Name | Explanation | Recommendation |
|---|---|---|---|
| 400 | Bad Request | This error occurs when there is an error in the connector configuration. |
Did you configure the connector correctly? |
| 401 | Unauthorized |
This error occurs when an authentication credential is invalid or when a user does not have sufficient privileges to access a specific API. |
Did you enter your credentials correctly? Are your credentials expired? Are your credentials entitled or licensed for that specific resource? |
| 403 | Forbidden | This error occurs when the permission or scope is not correct in a valid credential. |
Did you enter your credentials correctly? Do you have the required role or permissions for that credential? |
| 404 | Not Found | This error occurs when a URL path does not resolve to an entity. | Did you enter your API URL correctly? |
| 429 | Too Many Requests |
This error occurs when the API server receives too much traffic or if a user’s license or entitlement quota is exceeded. |
The server or user license/quota will eventually recover. The connector will periodically retry the query. If this occurs unexpectedly or too often, work with your API provider to investigate the server limits, user licensing, or quotas. |
For a full list of codes, refer to HTTP response status codes.
Verifying Ingestion
To verify ingestion:
- Click Investigate | Threat Hunting. The Interflow Search tab appears.
- Change the Indices to Syslog. The table immediately updates to show ingested Interflow records.