Stellar Cyber API Architecture Overview 
The Stellar Cyber Platform delivers unified threat detection, investigation, and response capabilities across both SaaS and on-premises deployments. This topic describes the platform's API architecture, the layers that protect customer data, and the operational controls that keep the service reliable.
The platform exposes two APIs: an internal API used by the management web UI, and a public REST API for programmatic integration. Both APIs share the same authentication, authorization, and access scope model.
Key Principles
|
Principle |
Description |
|---|---|
|
Secure by Design |
Security controls are integrated throughout the platform architecture and development lifecycle. |
|
Defense in Depth |
Independent controls at the network, application, and data layers reduce the impact of any single failure. |
|
Tenant Isolation |
Each customer's data and configuration is logically isolated and never shared across tenants. |
|
Continuous Observability |
Security-relevant requests and operational events are logged, monitored, and auditable. |
High-Level Architecture
The Stellar Cyber Platform is organized as a set of independent domain services behind a centralized API gateway. All client traffic routes through the gateway, which enforces transport security, validates requests, and directs traffic to the appropriate downstream service. A dedicated authentication and authorization service ensures security policies are applied consistently across the platform.
Public REST API endpoints are available at versioned paths in the following format:
https://<platform-host>/connect/api/v1/<endpoint>
API definitions are documented using an OpenAPI specification available both within the platform (under ? > API Docs) and here in the Knowledge Base.
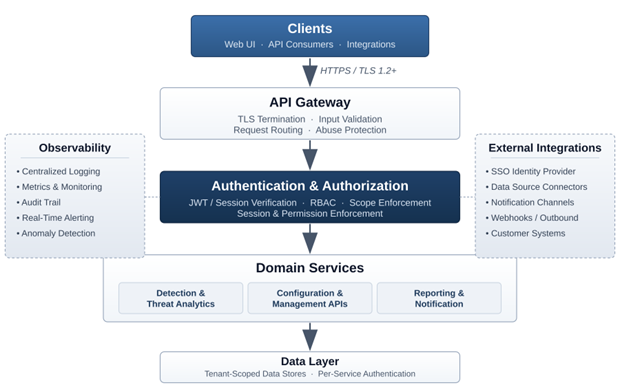
Architectural Layers
|
Layer |
Description |
|---|---|
|
API Gateway |
The centralized, hardened entry point for all API traffic. Terminates TLS, validates requests, and routes traffic to the appropriate domain service. |
|
Authentication & Authorization |
Verifies credentials (JWT or session cookie), resolves identity and effective access scope, and enforces RBAC policies. |
|
Domain Services |
Independent services for detection and analytics, configuration and management, and reporting and notification. Each service enforces its own domain-level authorization within the caller's authenticated tenant and user context. |
|
Data Layer |
Tenant-scoped data stores and search infrastructure. Each domain service authenticates to its data layer using service-specific credentials. |
Authentication, Authorization & Access Scope
Identity and access control are the foundation of the platform's security model. All customer-facing API requests pass through a centralized authentication and authorization pipeline before reaching domain services or customer data.
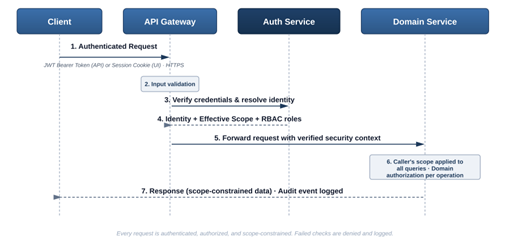
Authentication
- The web UI uses cookie-based session authentication. SSO (SAML / OIDC) is supported for web UI users.
- The public API uses JWT bearer tokens, obtained by exchanging an API key at the dedicated /access_token endpoint. Tokens are short-lived.
- API keys are issued per user and scoped to that user's RBAC privileges and access scope. Public API authentication uses locally managed API credentials rather than interactive SSO flows.
Authorization
- Role-based access control (RBAC) provides fine-grained permissions per operation.
- Permission checks are enforced at the domain service layer to reduce the risk of privilege escalation.
- Access privileges can be configured at the feature group, feature, and individual function level, supporting least-privilege configurations including view-only and no-access profiles.
Access Scope & Tenant Isolation
The platform implements a three-tier access scope model:
|
Scope |
Description |
|---|---|
|
Tenant |
Access to a single tenant's data and configuration. |
|
Partner |
Administrative access across a defined group of customer tenants. |
|
Root |
Full administrative access, reserved for platform administrators. |
Every authenticated request resolves to the caller's effective scope, and data access is automatically constrained to that scope. Tenants are logically isolated at the data layer, and cross-scope access is restricted by enforced authorization controls.
Security Controls
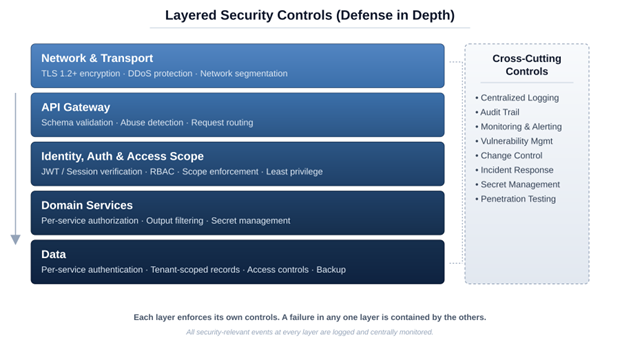
API Security
- Transport Security — All API traffic uses HTTPS with TLS 1.2 or higher. Weak ciphers and legacy protocols are disabled.
- OWASP-Aligned Testing — API security testing is designed with consideration for the OWASP API Security Top 10, with particular focus on authentication, authorization, input validation, and tenant isolation.
- Input Validation — API requests are validated at the gateway and re-validated at service boundaries.
- Abuse Protection — Abnormal request patterns and authentication failures are detected and surfaced through monitoring.
Operational Controls
- Logging & Audit — Application, security, and access events are collected centrally and retained per policy. Security-relevant events form a retained, centralized audit trail.
- Monitoring & Alerting — Real-time metrics drive automated alerting, and on-call engineers respond to critical issues.
- Vulnerability Management — Dependencies and base images are continuously scanned, and remediation is prioritized by severity.
- Change Management — Code review, automated testing, and progressive rollout govern every change to the platform.
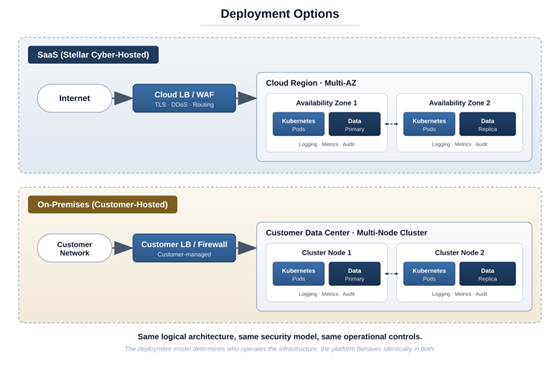
Deployment Models
The Stellar Cyber Platform supports two deployment models. Both share the same logical API architecture, security model, and operational controls. They differ in where the platform runs and who manages the underlying infrastructure.
|
Model |
Description |
|---|---|
|
SaaS |
The platform is hosted in a major public cloud and fully operated by Stellar Cyber. |
|
On-Premises |
The platform is installed in the customer's own environment and operated by the customer. The customer governs access to their own infrastructure and data. |
Data Protection
- All customer data is encrypted in transit using HTTPS / TLS. Domain services authenticate to their data stores using service-specific credentials.
- Backups are taken on a regular schedule and verified for integrity.
- Access to production data is restricted to authorized personnel under documented controls. In on-premises deployments, the customer governs access to their own environment.
