Introducing the Stellar Cyber API 
Stellar Cyber provides a public API that lets you interact with the product programmatically, allowing you to write your own scripts to retrieve data from the product or create entities within it.
-
Stellar Cyber is always adding new public APIs to the product. The Summary of Public APIs, below, shows you the types of information you can retrieve and create.
-
Once you are ready to get started working with the API, use the following steps:
-
Use the information in Configuring API Authentication to create a user with the necessary privileges and an API key.
-
Use the detailed reference material from the API's swagger.json file to create your own scripts and API calls.
-
-
Refer to the Stellar Cyber Public API Examples for a set of sample scripts and API calls that you can use as inspiration for your own work.
Access to the API is only available using local user accounts. Single-sign on (SSO) users cannot access the API with their SSO credentials.
The API replaces access to port 8889 on the DP.
Creating and Testing Public API Calls 
You can create and test sample API calls on your Stellar Cyber Platform by clicking the ? | API Docs option, as shown below:
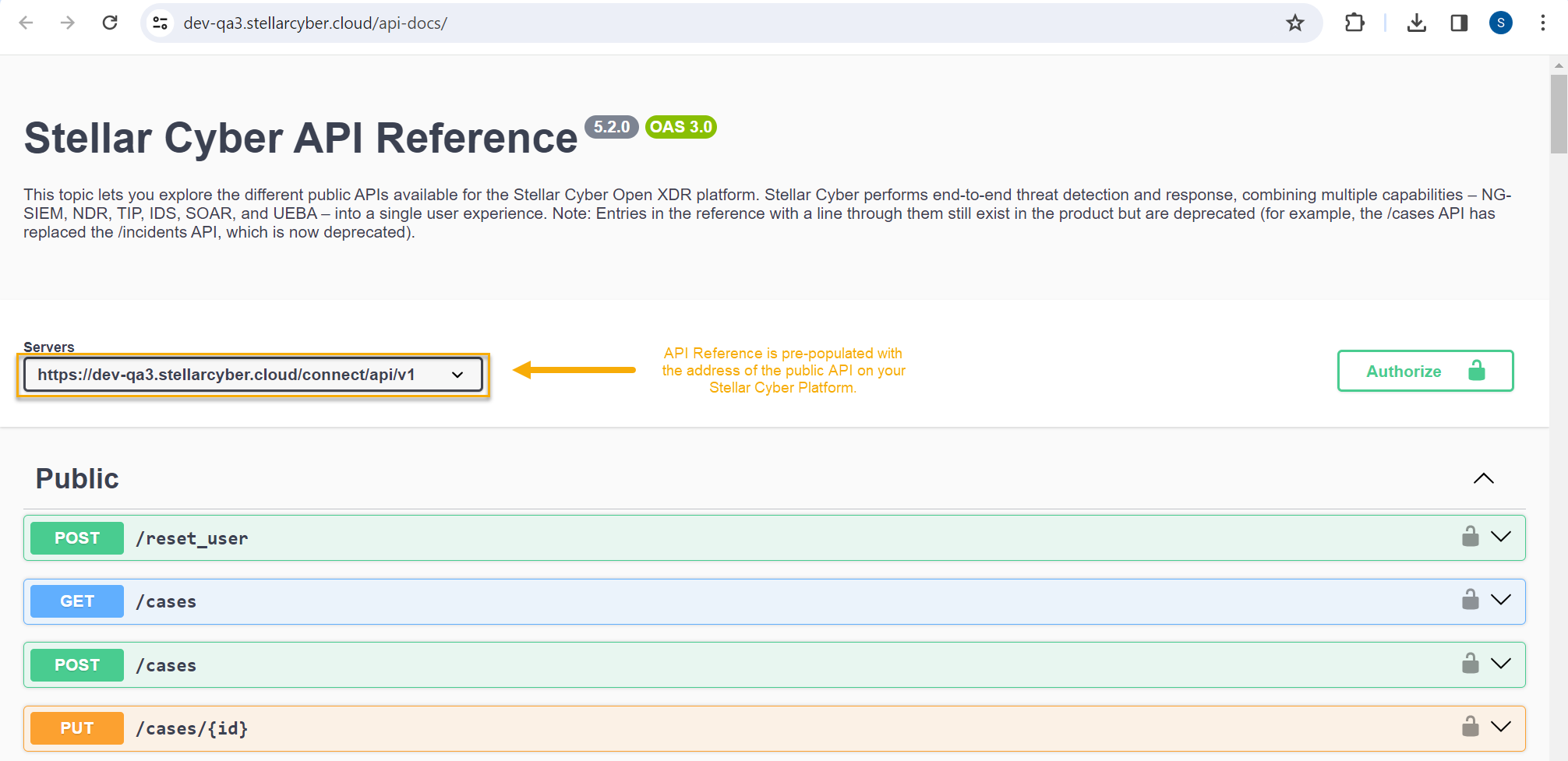
In response, a new browser tab appears with an interactive Swagger reference pre-populated to use the API on your Stellar Cyber Platform.
Authenticating with the API Test Page
Before you can test sample API calls, you'll need to obtain an API key from the Stellar Cyber user interface and use it to generate a JWT token in the Swagger reference. Then, you can use the generated JWT token to access all other parts of the API (only the /access_token API works with simple API key authentication; everything else requires a JWT token).
Keep in mind that only user accounts with a Scope of root and a User Privilege of Super Admin can use the API Reference to test live API calls.
Use the following procedure to authenticate with the interactive Swagger reference:
-
Start by generating an API key in the System | Users page:
-
Navigate to System | Users.
-
Locate the user account to perform the API call and select Edit () in its row.
Remember that the user performing the call must have Root scope and Super Admin privileges.
-
Locate the API Access item in the dialog box that appears and select Generate New Token.
-
Copy and paste the API key into a text file to store it temporarily.
-
-
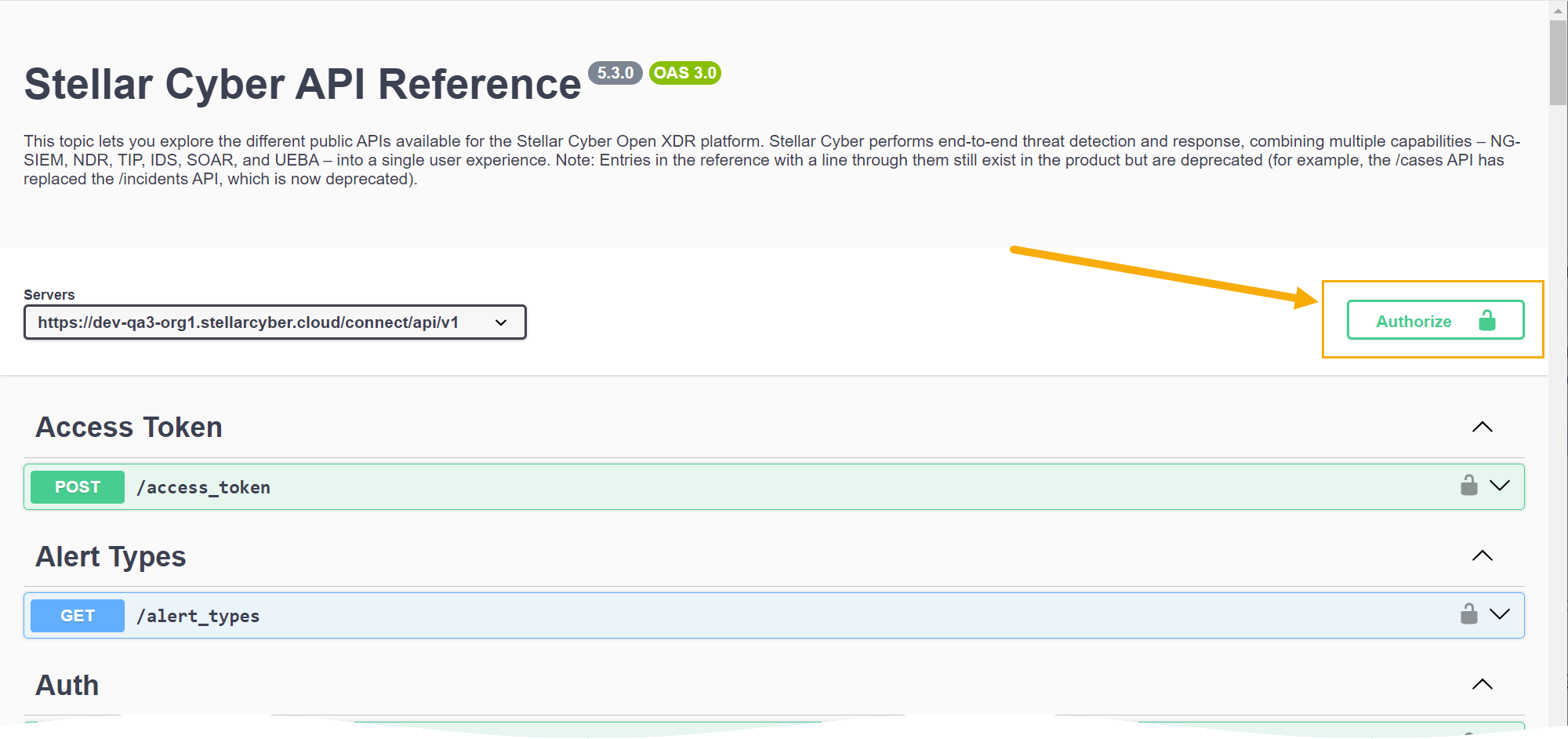
Navigate to ? | API Docs and click the Authorize button at the top right, as illustrated below.
-
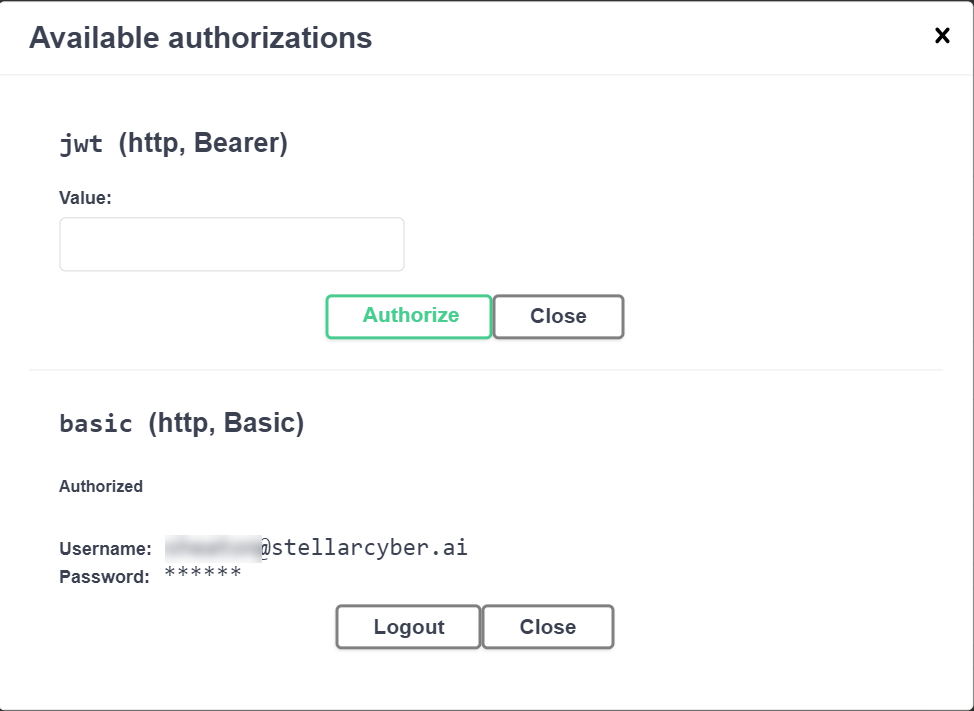
Locate the basic (http, Basic) fields at the bottom of the Available authorizations dialog box. Enter your username and paste in the API key you copied from the System | Users page in the corresponding fields here.
-
Click the Authorize button below the basic fields. You are now logged in using basic authentication, as illustrated below:
-
Click the x in the upper right hand corner of the Available authorizations dialog box to close it.
-
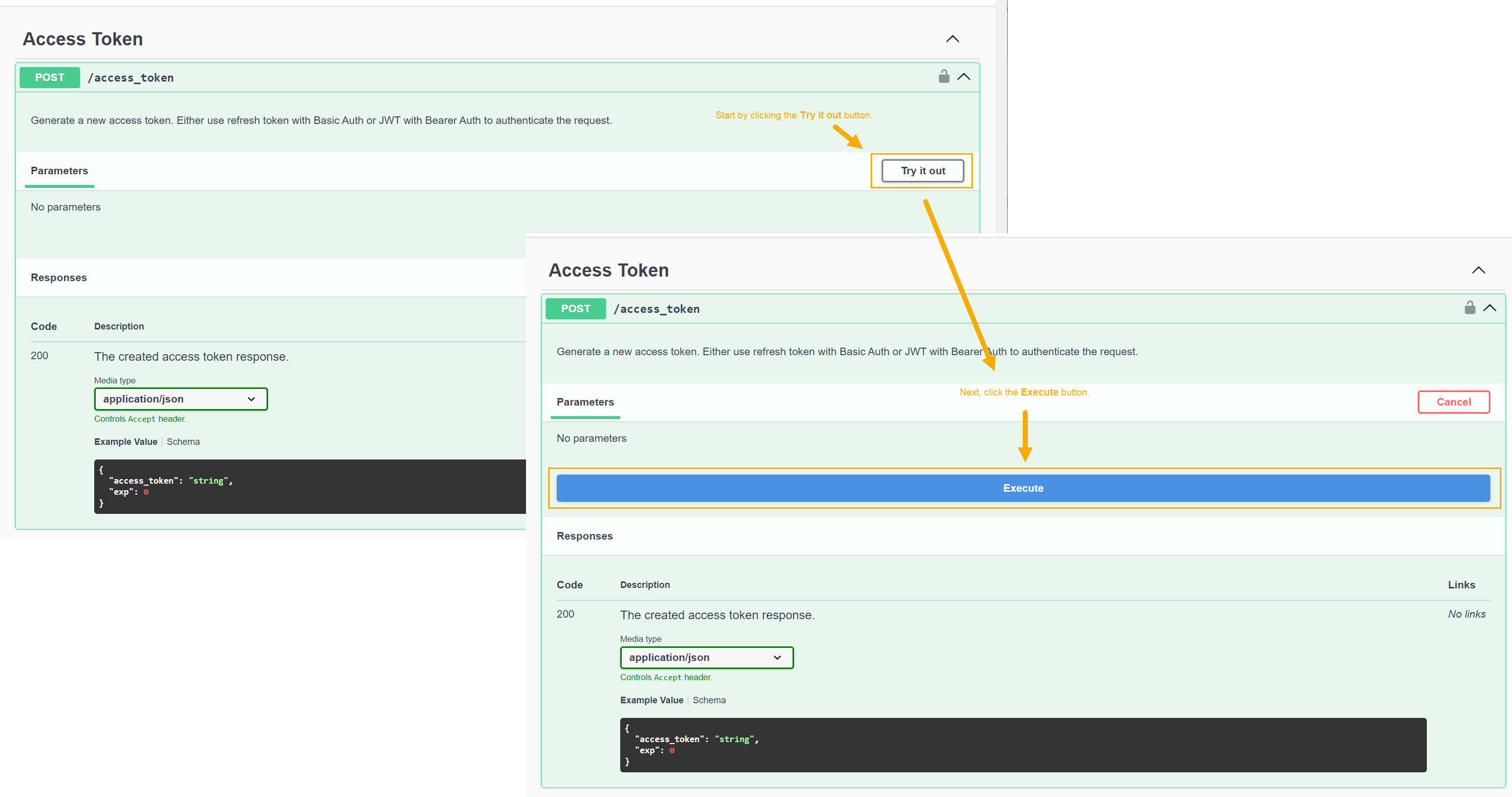
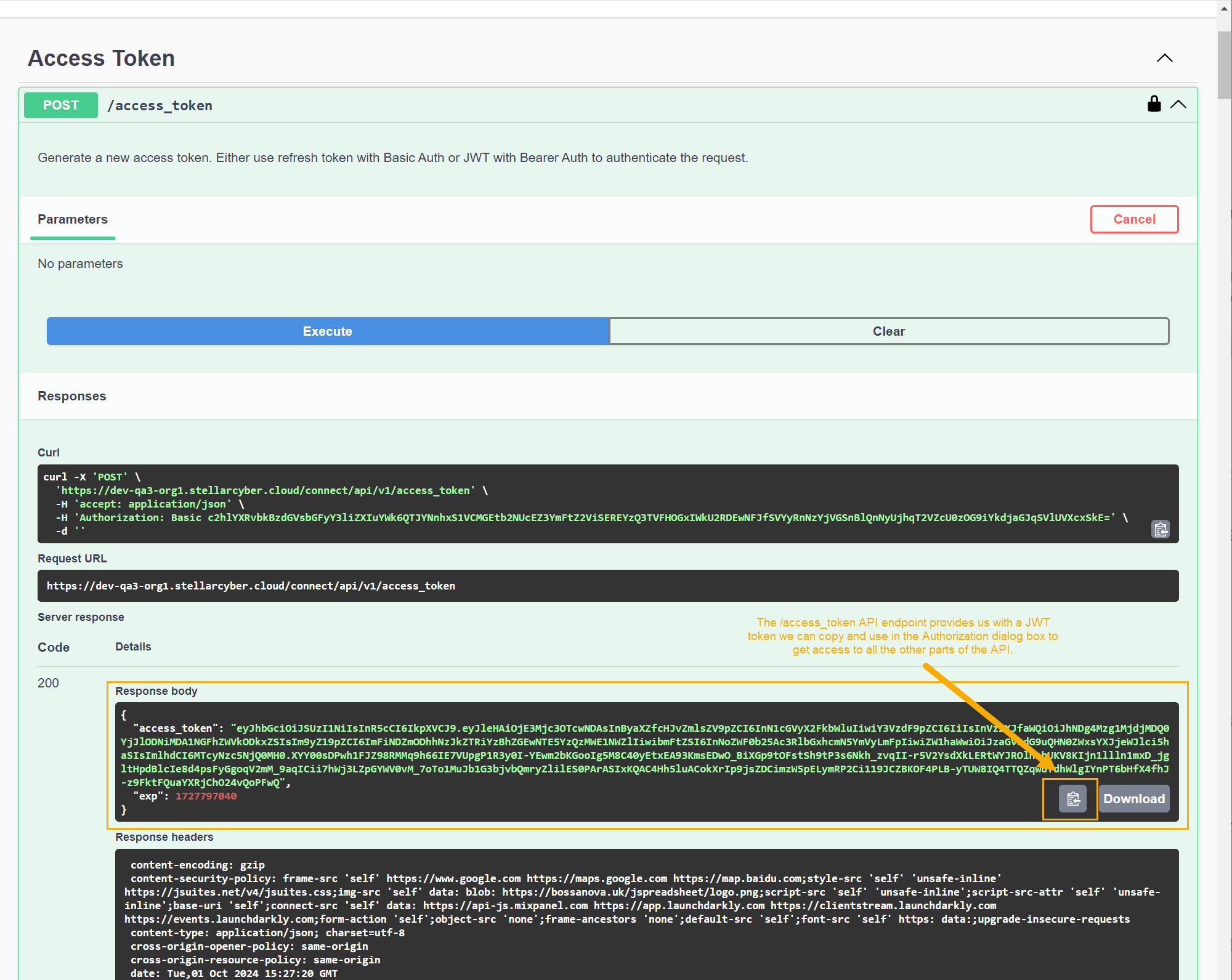
Cascade open the Access Token entry in the API Test Page. Then click Try it out and Execute, as illustrated below:
-
In response, the
/access_tokenAPI endpoint provides us with a JWT access token, as illustrated below. Use the Copy button in the Response body pane to copy the JWT token to the clipboard, as illustrated below.
in the Response body pane to copy the JWT token to the clipboard, as illustrated below.You can also copy the JWT token manually by selecting the green portion of the Response body between quotation marks. However, the Copy button is typically more reliable.
-
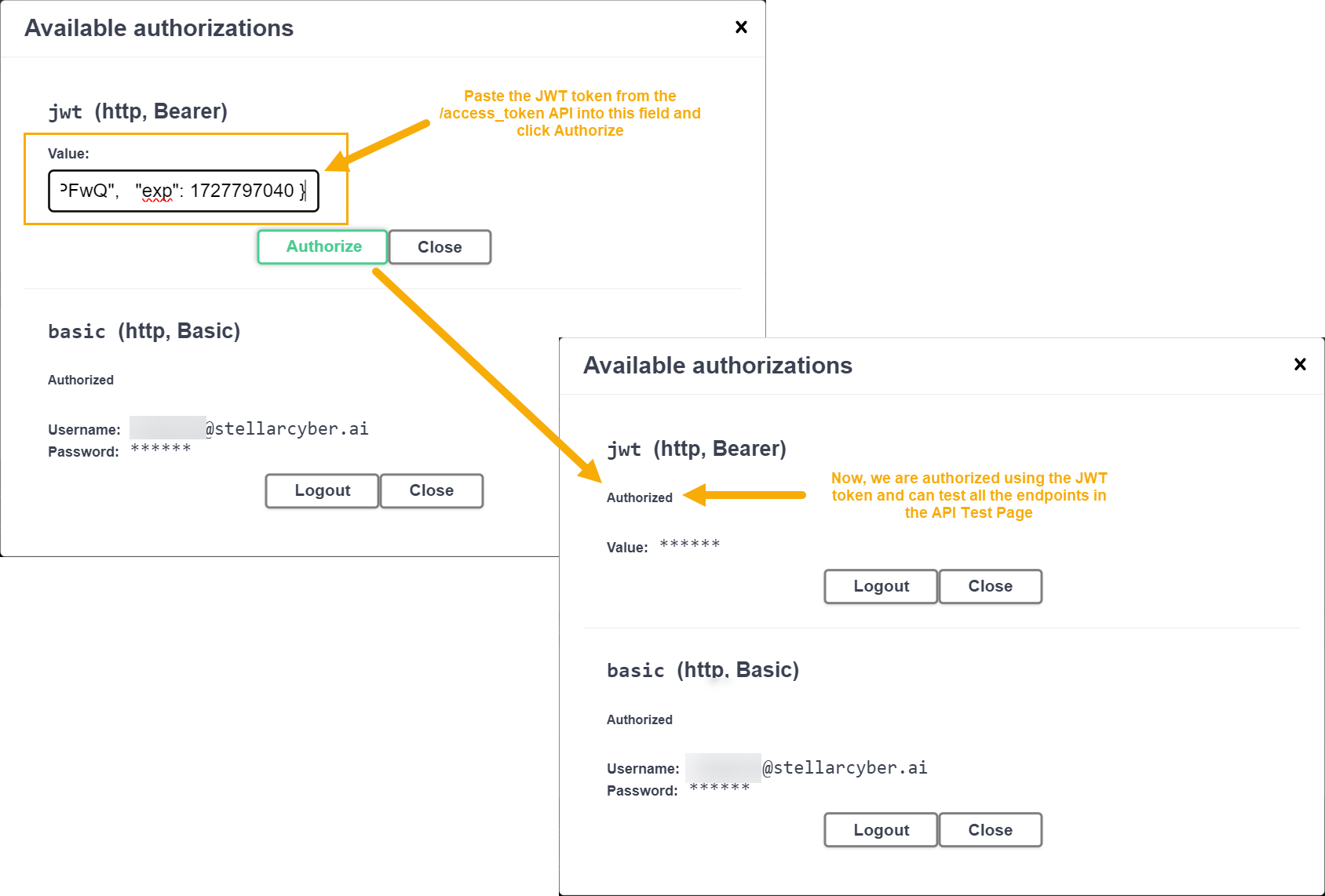
Click the Authorize button at the top right of the API Test Page again.
-
Paste the token you copied from the Response body pane into the jwt (http, Bearer) field and click Authorize, as illustrated below.
At this point, you are authorized to the API Test Page using a JWT token and can test out the other endpoints in the API Test Page.
About JWT Token Expiration
Keep in mind that JWT tokens are configured by default to expire ten minutes after they are generated. If this happens while you are using the API Test Page, you may notice that your test calls are no longer working. You can fix this by generating a new JWT token from the /access_token endpoint using the steps in the procedure above. Then, click Authorize, log out of the jwt (http, Bearer) section and log back in with your new JWT token.
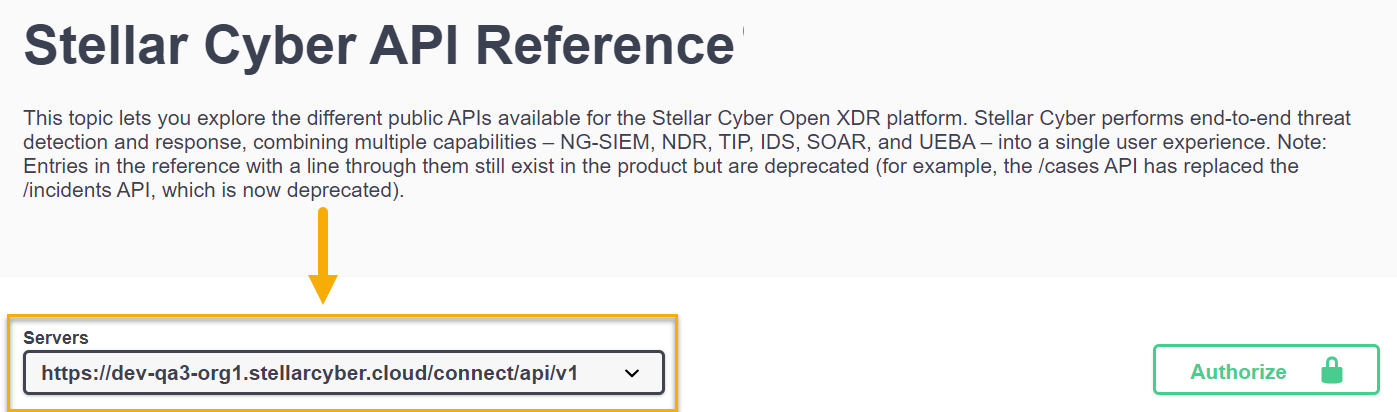
Relative Path to Stellar Cyber API Endpoints
The relative path to Stellar Cyber's public API endpoints is as follows:
-
https://<Platform Hostname>/connect/api/v1/<specific endpoint>
You can see this at the top of the Stellar Cyber API Reference in the Servers field. For example:
The individual endpoints shown in the API Reference do not include the relative path, but you must include it when accessing the public API outside of the swagger.json page.
Summary of Public APIs
As summarized in the interactive API Reference, Stellar Cyber provides public APIs for the following features:
-
Create, delete, edit, and list connectors. You can also edit the checkpoint of a connector – the time from which it pulls data, which is useful in case of data loss.
When numerous connectors roll back checkpoints during regular operating hours, it can lead to increased resource consumption and potential process interruption due to circuit breakers. Consult with Customer Support for considerations regarding off-peak execution of checkpoint rollback.
-
Get alert types along with their key fields

-
Retrieve phonehome logs

-
Retrieve privilege profiles so they can be used with create/update user APIs

-
Download sensor images

-
Retrieve detailed sensor information
-
Delete sensors
-
Retrieve detailed case information
-
Retrieve case observables
-
Update case information
-
Create cases
-
Retrieve information on storage usage
-
Retrieve ingestion statistics
-
Retrieve information on the configuration and hits of log filters.
-
Retrieve user activity logs for Stellar Cyber user accounts.
-
Create, delete, update, and list tenants
-
Create, Delete, Update, and List Tenant Groups
-
Update Tags, Status, and Comments for Events
-
Perform an ElasticSearch Query on a Specific Index
-
Reset User Passwords
-
Add events to the Security Index (bulk or standard)
-
Create, Delete, and List Lookup Tables (by Tenant or by All Tenants)
-
Create, Delete, and List Reports
-
Create, Delete, and List Security Event Filters
-
Create, Modify, and Delete Data Analyzer Profiles