Configuring Office 365 Reporting Web Service Connectors
This connector allows Stellar Cyber to ingest logs from Office 365 Reporting Web Service and add the records to the data lake. It integrates with the Microsoft Reporting Web Service to query Message Trace data.
Note the following:
-
This connector is set to start retrieving data from 24 hours ago due to a limitation from Microsoft that data may be delayed by up to 24 hours before they appear in a report. The connector ingestion interval is every 5 minutes.
-
This connector gets 2000 records for each time window query. (By default, the window is 10 minutes range.)
Stellar Cyber connectors with the Collect function (collectors) may skip collecting some data when the ingestion volume is large, which potentially can lead to data loss. This can happen when the processing capacity of the collector is exceeded.
Connector Overview: Office 365 Reporting Web Service
Capabilities
-
Collect: Yes
-
Respond: No
-
Native Alerts Mapped: No
-
Runs on: DP
-
Interval: Configurable
Collected Data
|
Content Type |
Index |
Locating Records |
|---|---|---|
|
Message Trace |
Windows Events |
Domain
|
<Authentication Endpoint> where <Authentication Endpoint> is a variable from the configuration of this connector and will be one of the following, based on the Subscription Plan:
|
Response Actions
N/A
Third Party Native Alert Integration Details
N/A
Required Credentials and Configurations
-
Authentication Endpoint, Directory ID, Application ID, and API Access Key
Adding an Office 365 Reporting Web Service Connector
To add an Office 365 Reporting Web Service connector:
Obtaining Office 365 Reporting Web Service Credentials
Before you configure the connector in Stellar Cyber, you must obtain the following Office 365 Reporting Web Service credentials:
-
Authentication Endpoint—The authentication endpoint, which you can select from the dropdown menu.
-
Directory ID—The tenant from which to request permission, also known as the Tenant ID.
-
Application ID—The ID that the app registration portal assigned when the app was registered, also known as the Client ID.
-
API Access Key—The API access key or client secret that you generated for your app in the app registration portal, also known as the Client Secret.
For details, see Registering the Application and Obtaining Permissions.
Registering the Application
Follow the guidance in the Microsoft documentation to get started with Reporting Web Service.
To register the application in Microsoft Entra ID (formerly Azure Active Directory) and obtain the Tenant ID, Client ID, and Client Secret:
-
Log in as an administrative user to the Azure Management Portal at https://portal.azure.com and sign in with the credentials for the tenant subscribed to Office 365.
-
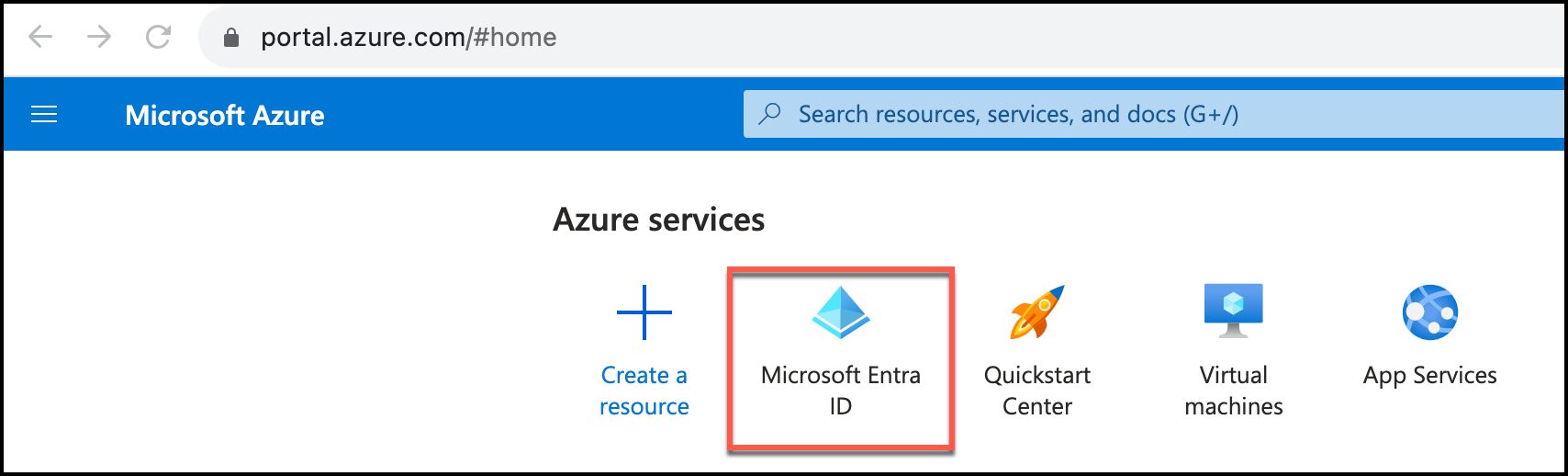
From Azure services, select Microsoft Entra ID.
-
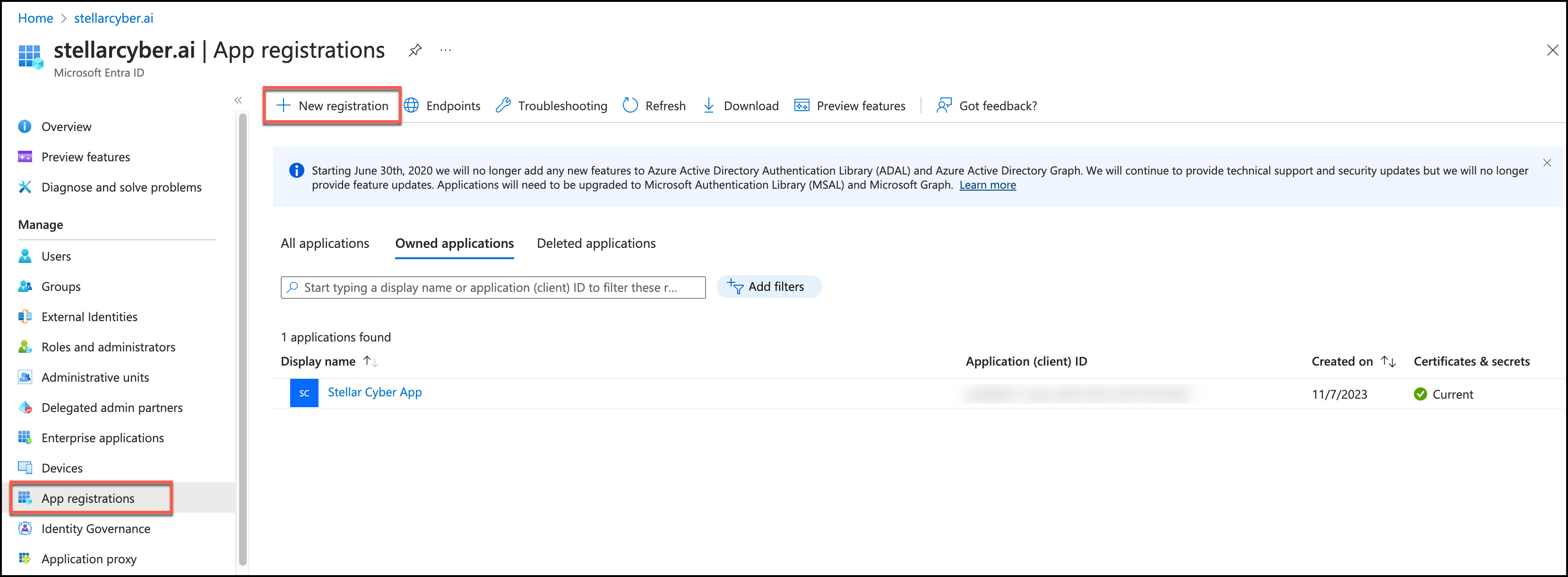
In the navigation pane, select App registrations.
-
Click New registration.
-
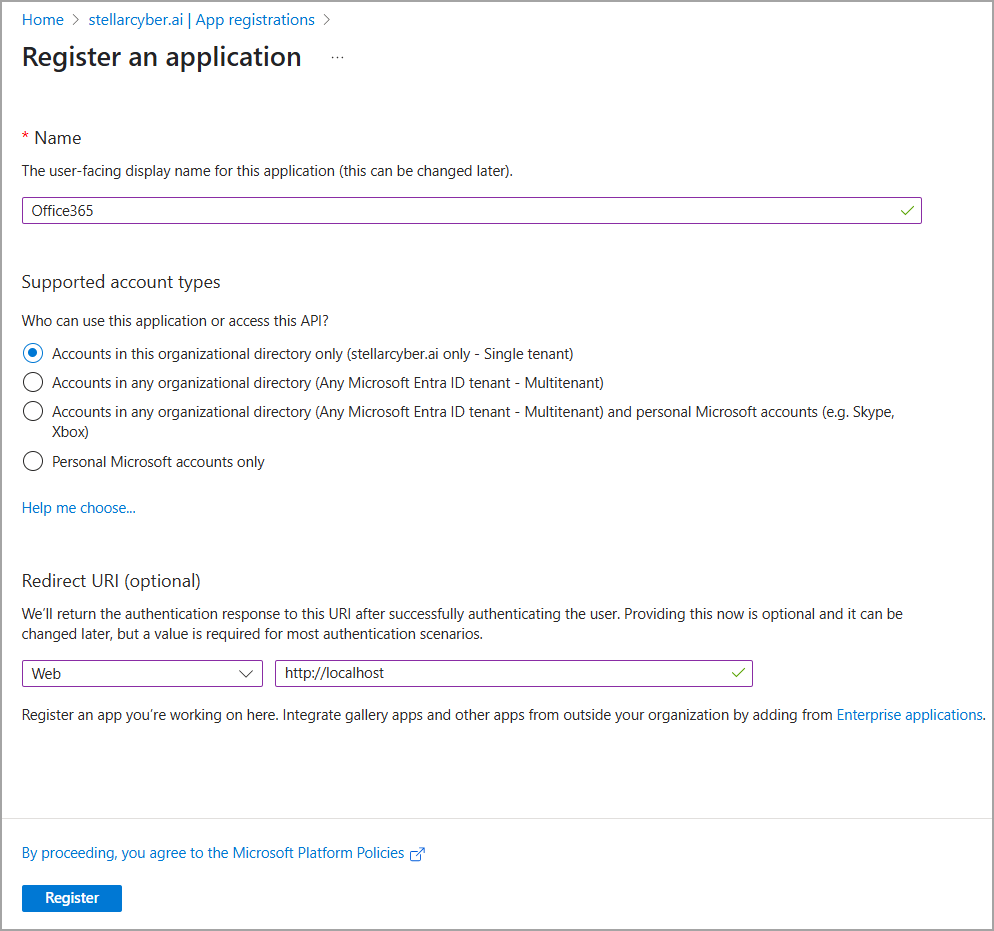
In Register an application, enter a Name.
-
Choose a supported account type. For Single tenant, select Accounts in this organizational directory only.
-
For Redirect URI (optional), select Web, and enter
http://localhostas the Web URL. -
Click Register.
-
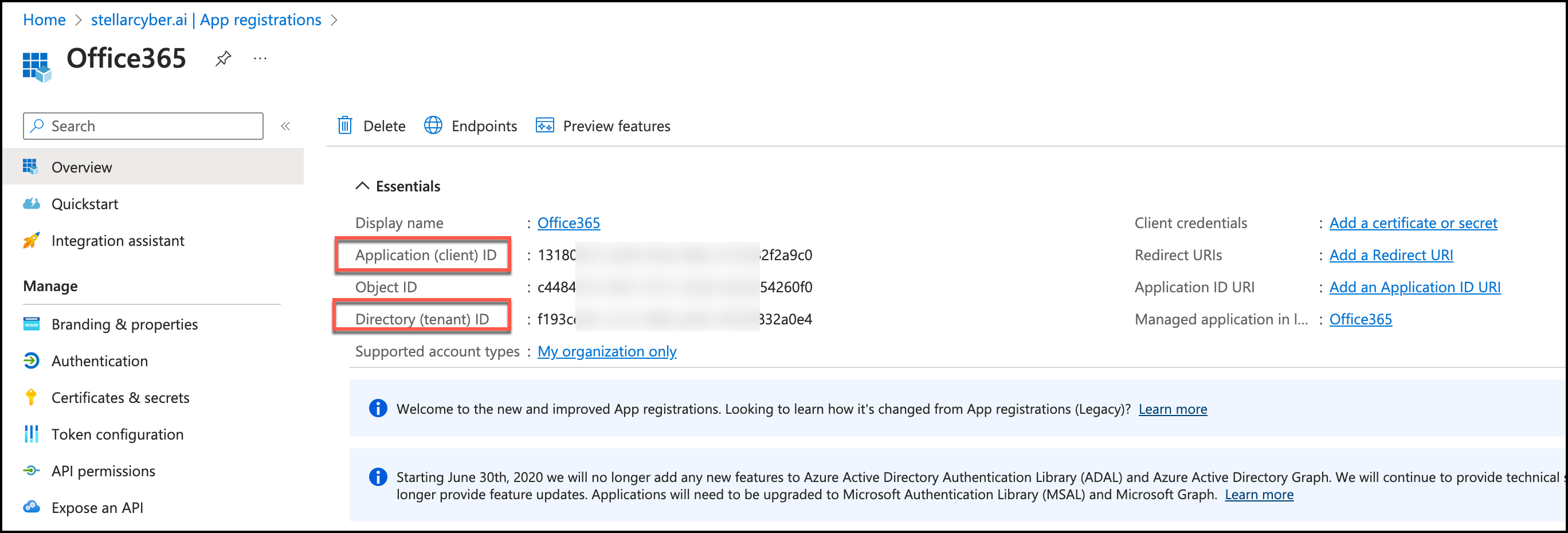
Copy the Application (client) ID and Directory (tenant) ID. You will use them to configure the connector in Stellar Cyber.
-
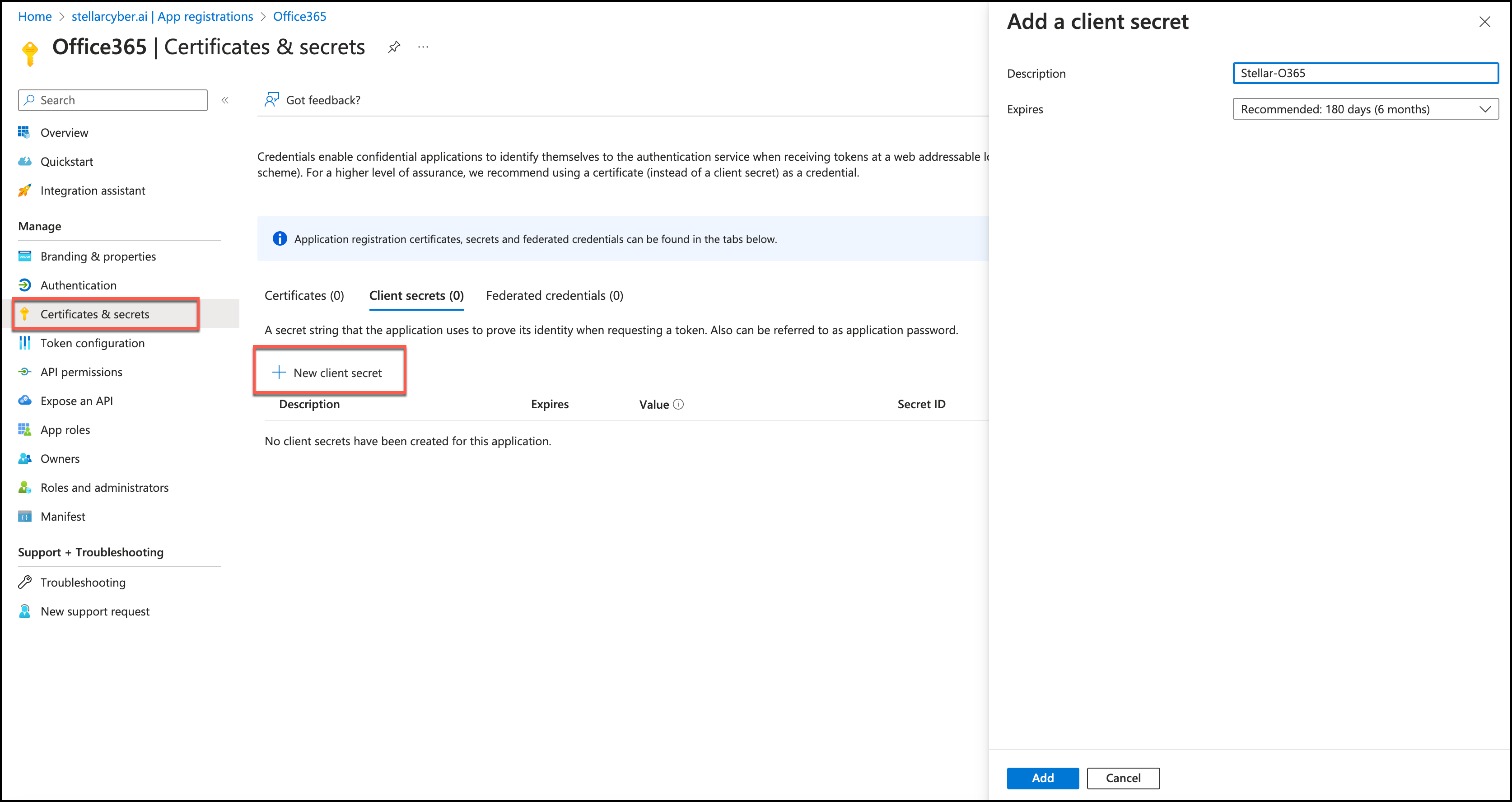
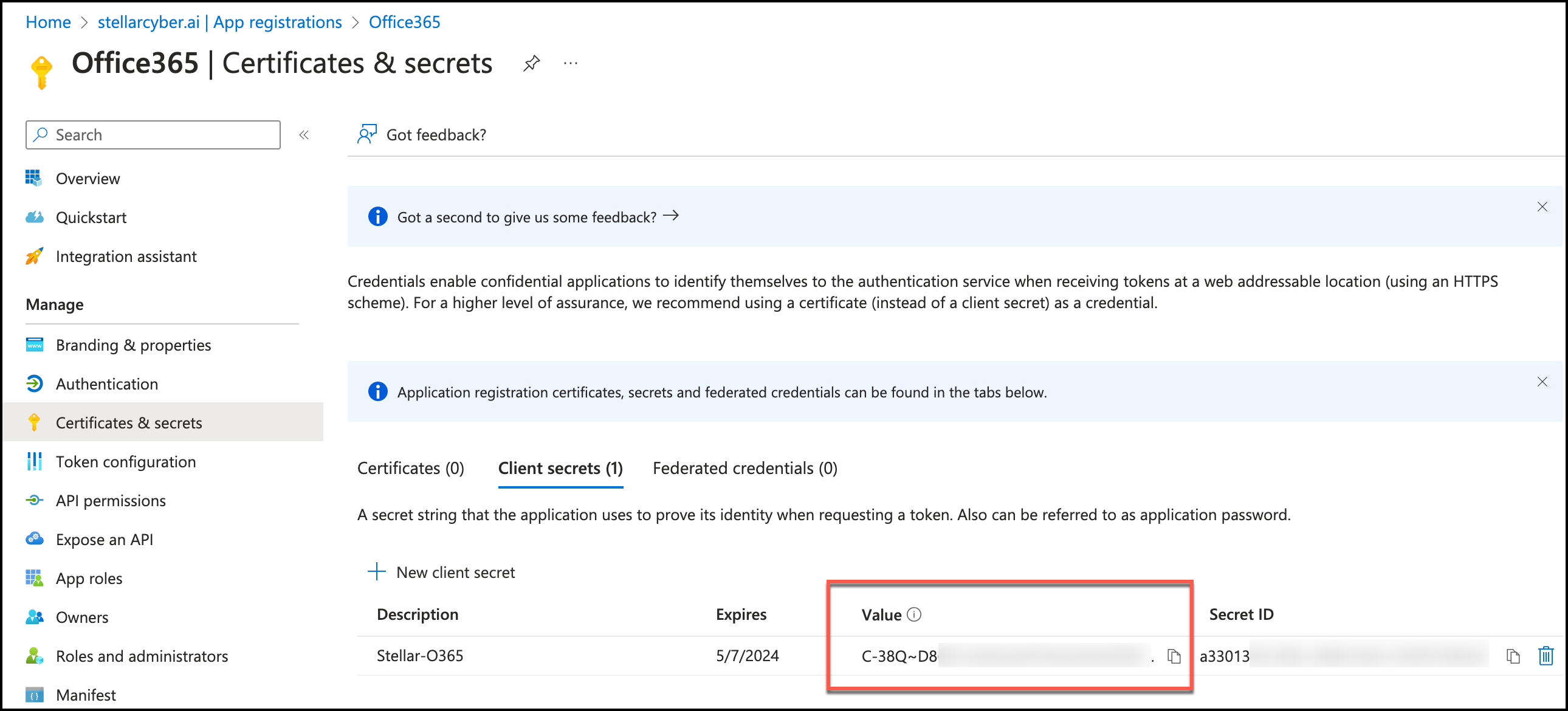
In the navigation pane, click Certificates & secrets.
-
Click New client secret.
-
In Add a client secret, enter a Description and choose an expiration.
-
Click Add.
-
Copy the Value. You will use this as the API Access Key to configure the connector in Stellar Cyber.
Store the value in a safe location. It cannot be retrieved later.
Obtaining Permissions
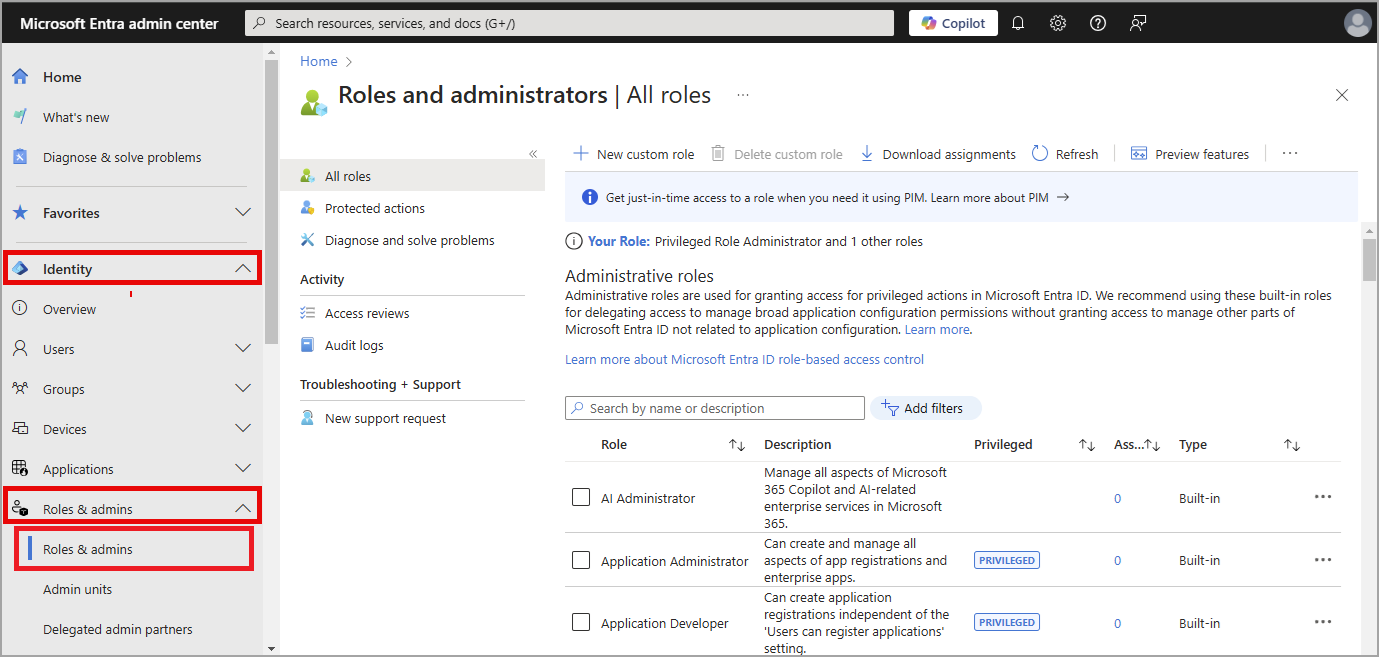
First, assign the Security Reader role to the created application.
-
Log in to the Microsoft Entra ID admin center.
-
Navigate to Identity > Roles & admins > Roles & admins.
-
Search or scroll for the Security Reader role in the Administrative roles and select it.
-
Click Add assignments and select the users or groups you want to assign to this role.
-
Click Add to assign the role.
Next, add API permissions for your application.
-
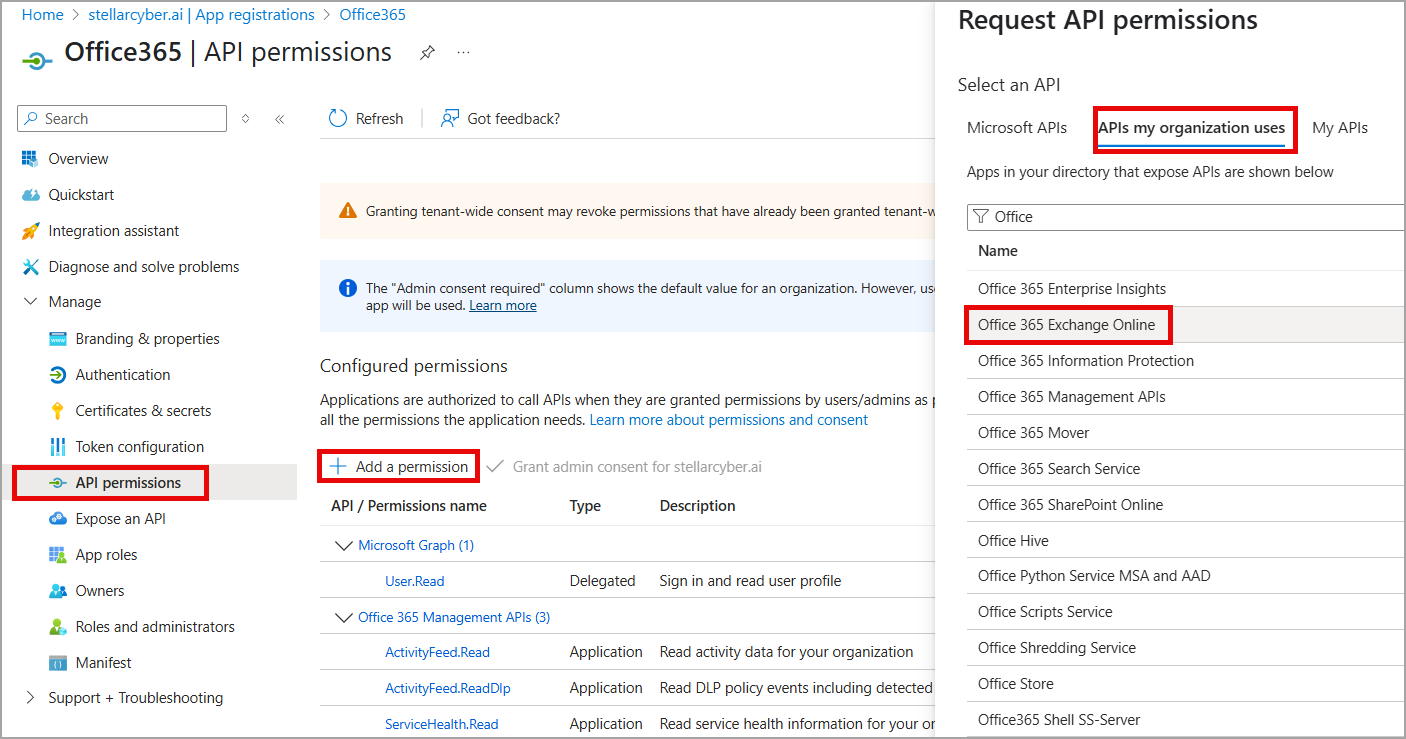
In the navigation pane, select API Permissions.
-
Click Add a permission.
-
In Request API permissions, select the APIs my organization uses tab.
-
Search or scroll for Office 365 Exchange Online, and select it.
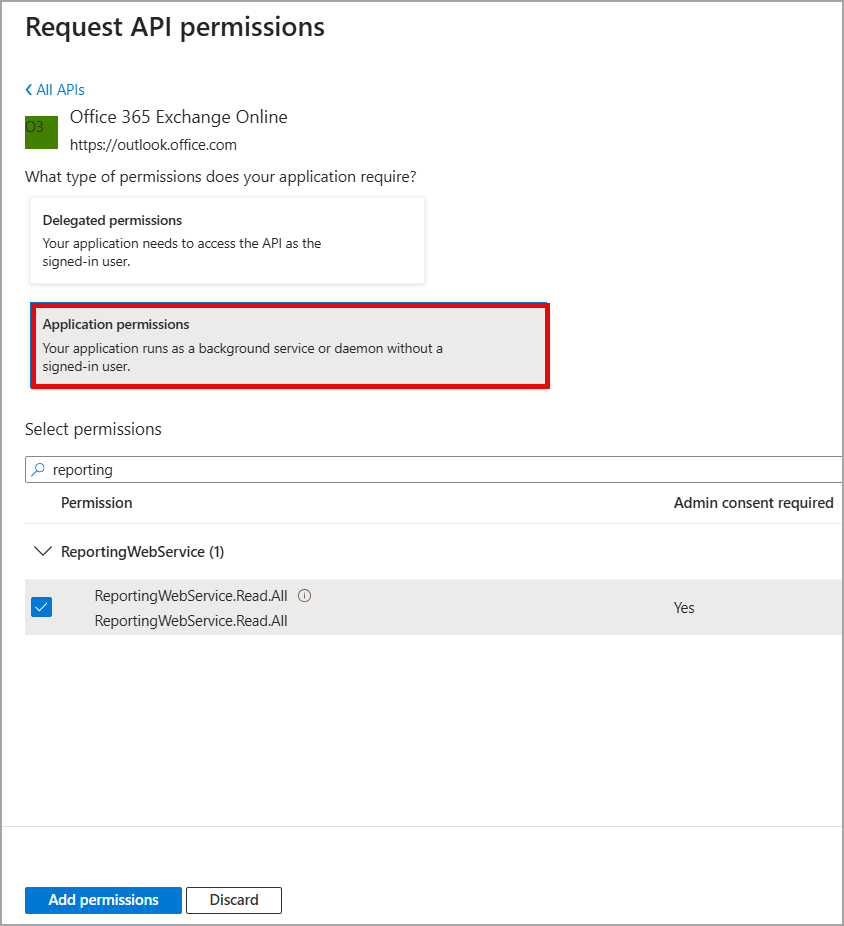
Next, select Application Permissions:
-
Select Application Permissions to allow the application to run as a background service without a signed-in user.
-
Search for and select ReportingWebService.Read.All.
-
Click Add permissions.
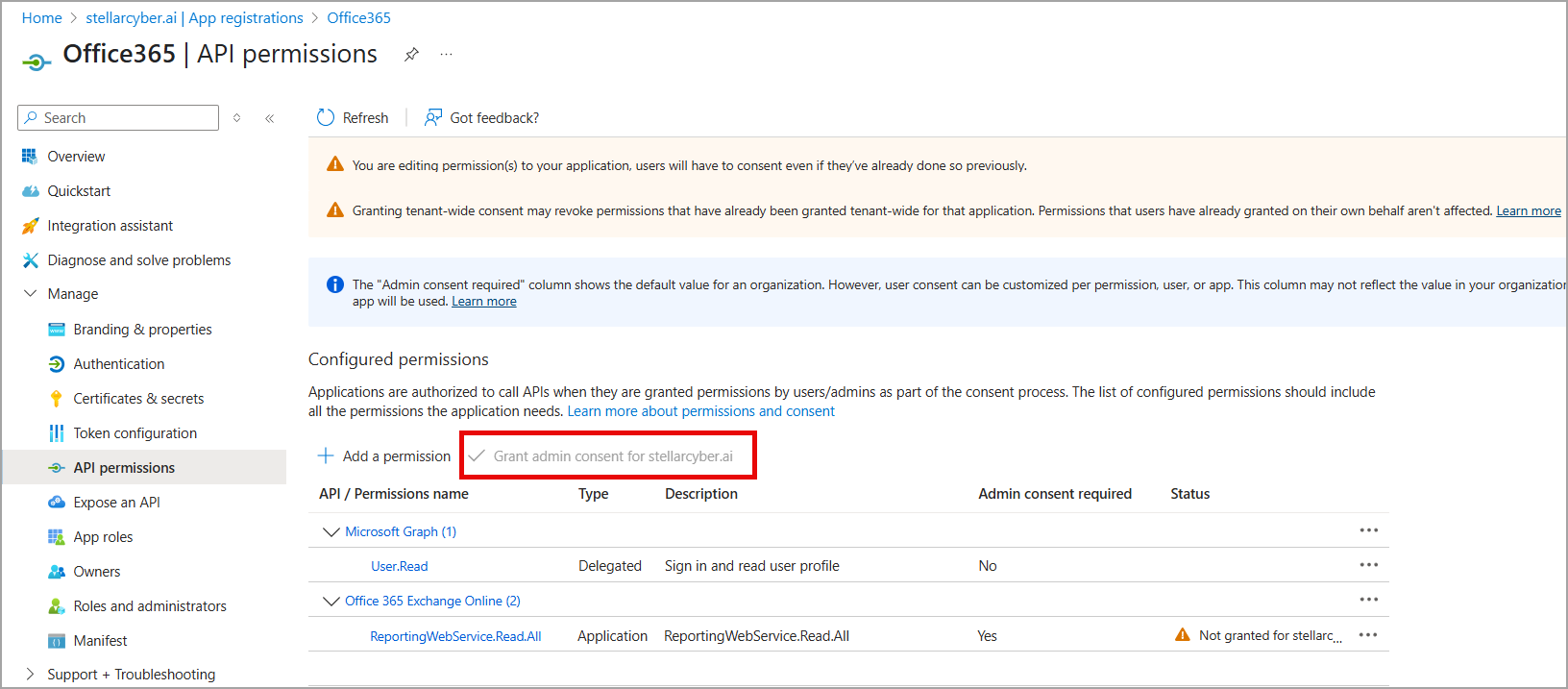
Then, grant admin consent.
-
After adding permissions, there is a banner at the top of the API Permissions page that says the permissions require admin consent.
-
In the API permissions window, go to the Grant admin consent section.
-
If you are the Office 365 super admin, grant the permissions. Select the checkmark to Grant admin consent for <tenant name>.
-
Confirm the consent by clicking Yes.
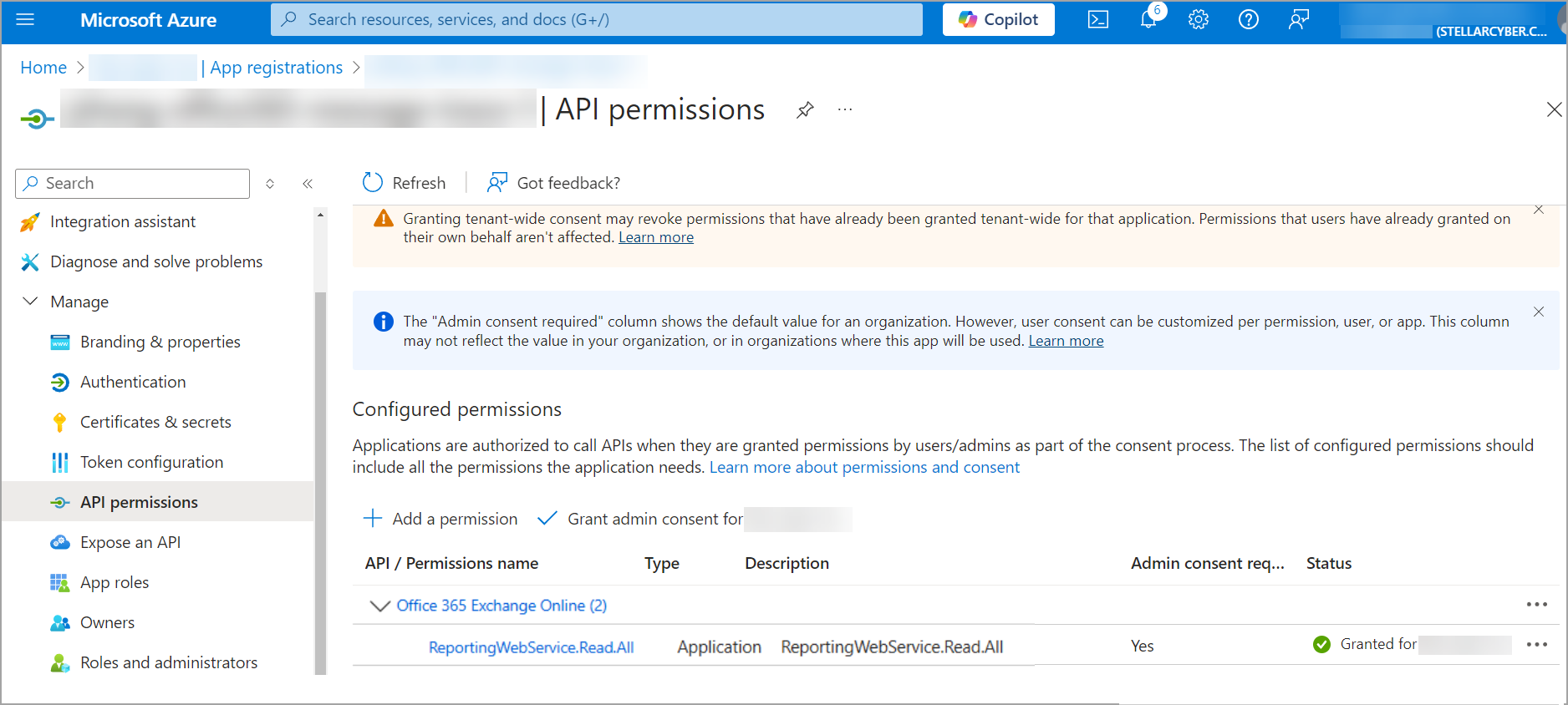
Finally, verify the permissions.
-
After granting admin consent, the status for the permissions will update to Granted for < tenant name>.
-
Ensure that the Application permission (ReportingWebService.Read.All) is correctly listed and granted.
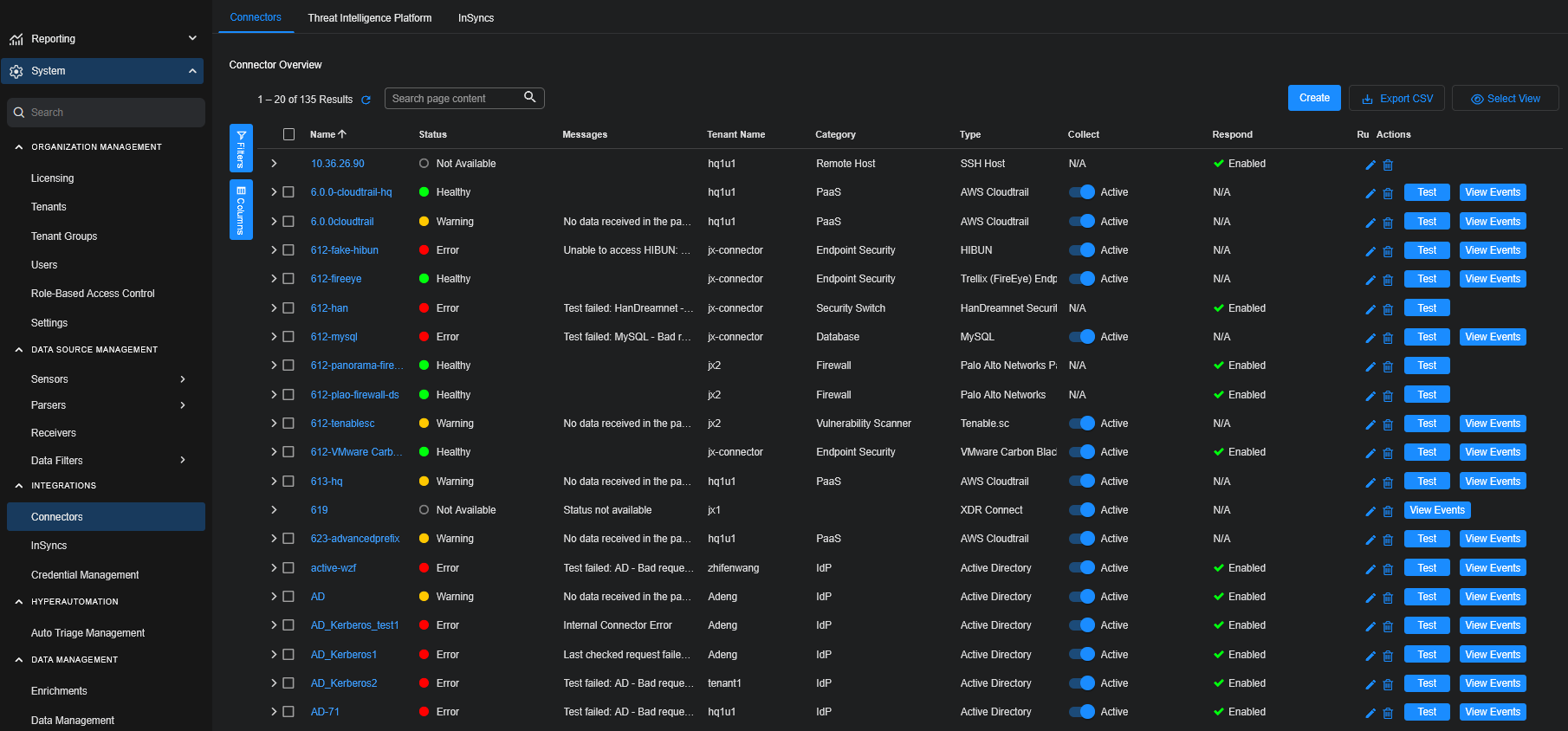
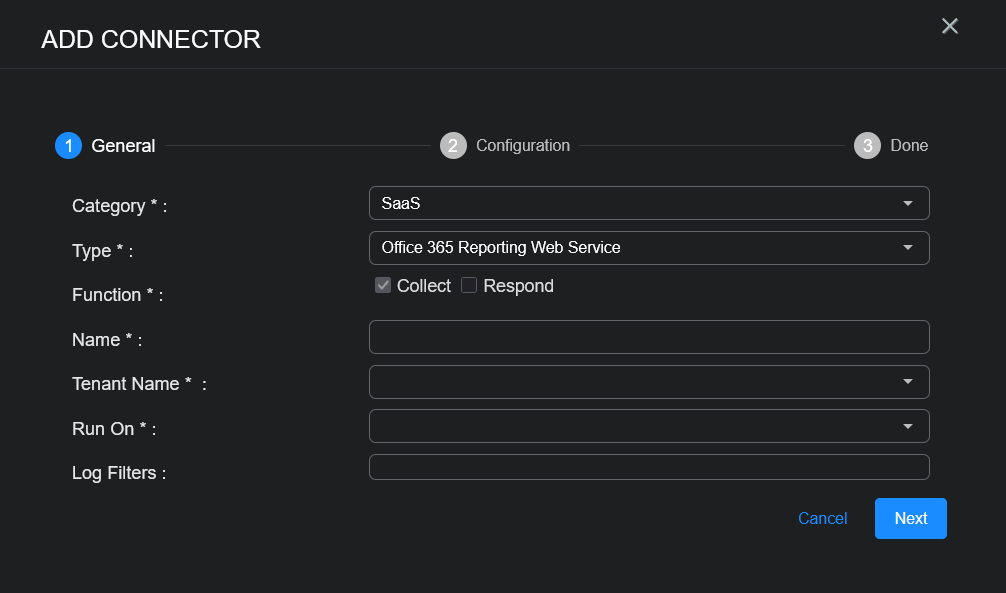
Adding the Connector in Stellar Cyber
To add an Office 365 Reporting Web Service connector in Stellar Cyber:
-
Log in to Stellar Cyber.
-
Click System | INTEGRATIONS | Connectors. The Connector Overview appears.
-
Choose SASE from the Category dropdown.
-
Choose Office 365 Reporting Web Service from the Type dropdown.
The asterisk (*) indicates a required field.
-
For this connector, the supported Function is Collect, which is enabled already.
-
Enter a Name.
Notes:- This field does not accept multibyte characters.
- It is recommended that you follow a naming convention such as tenantname-connectortype.
-
Choose a Tenant Name. The Interflow records created by this connector include this tenant name.
-
Choose the device on which to run the connector.
-
(Optional) When the Function is Collect, you can apply Log Filters. For information, see Managing Log Filters.
-
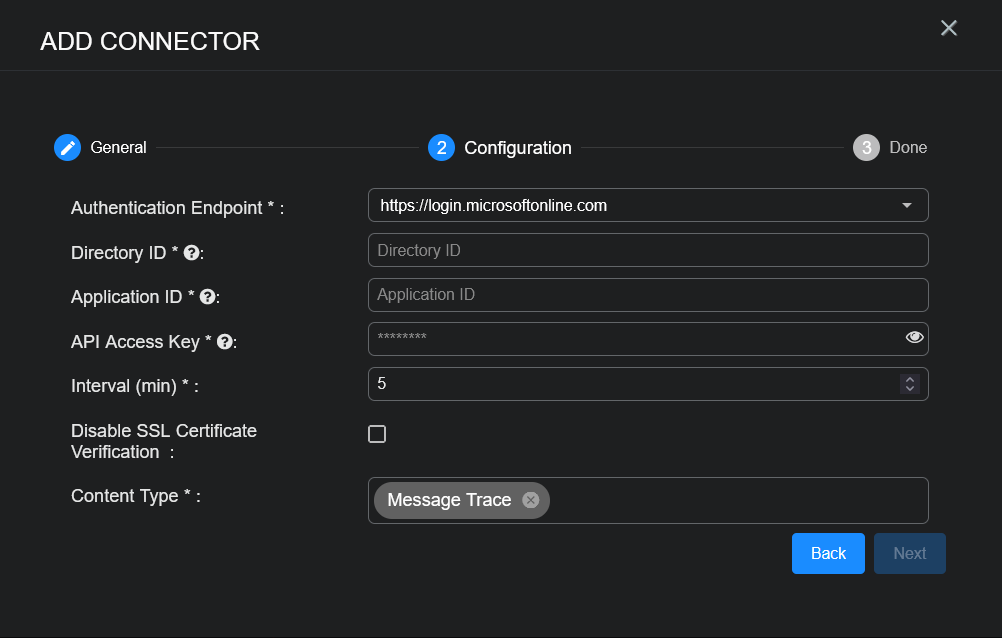
Click Next. The Configuration tab appears.
The asterisk (*) indicates a required field.
-
Enter the Authentication Endpoint you noted above in Obtaining Office 365 Reporting Web Service Credentials.
-
Enter the Directory ID you noted above.
-
Enter the Application ID you noted above.
-
Enter the API Access Key you noted above.
-
Choose the Interval (min). This is how often the logs are collected.
-
(Optional) Click Disable SSL Certificate Verification if you want to disable SSL certificate verification. Only disable SSL certificates if you have a reason to, otherwise, it is not a good security practice.
-
Choose the Content Type you would like to collect. The logs for Message Trace are supported.
-
Click Next. The final confirmation tab appears.
-
Click Submit.
The new connector is immediately active.
Testing the Connector
In addition to testing for connectivity, the Test button for the Office 365 Reporting Web Service connector tests that the Authentication Endpoint, Directory ID, Application ID, and API Access Key are correct and data requests for the requested content type returns successful responses.
When you add (or edit) a connector, we recommend that you run a test to validate the connectivity parameters you entered. (The test validates authentication and connectivity).
For connectors running on a sensor, Stellar Cyber recommends that you allow 30-60 seconds for new or modified configuration details to be propagated to the sensor before performing a test.
-
Click System | INTEGRATIONS | Connectors. The Connector Overview appears.
-
Locate the connector by name that you added, or modified, or that you want to test.
-
Click Test at the right side of that row. The test runs immediately.
Note that you may run only one test at a time.
Stellar Cyber conducts a basic connectivity test for the connector and reports a success or failure result. A successful test indicates that you entered all of the connector information correctly.
To aid troubleshooting your connector, the dialog remains open until you explicitly close it by using the X button. If the test fails, you can select the button from the same row to review and correct issues.
The connector status is updated every five (5) minutes. A successful test clears the connector status, but if issues persist, the status reverts to failed after a minute.
Repeat the test as needed.
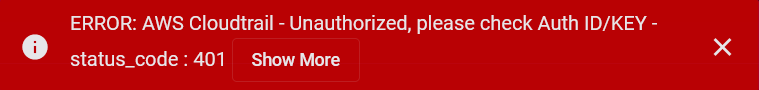
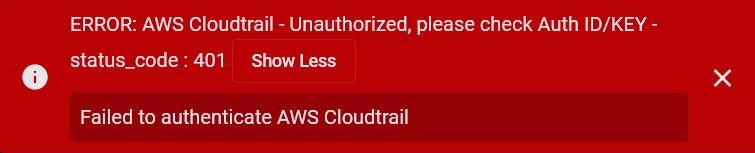
If the test fails, the common HTTP status error codes are as follows:
| HTTP Error Code | HTTP Standard Error Name | Explanation | Recommendation |
|---|---|---|---|
| 400 | Bad Request | This error occurs when there is an error in the connector configuration. |
Did you configure the connector correctly? |
| 401 | Unauthorized |
This error occurs when an authentication credential is invalid or when a user does not have sufficient privileges to access a specific API. |
Did you enter your credentials correctly? Are your credentials expired? Are your credentials entitled or licensed for that specific resource? |
| 403 | Forbidden | This error occurs when the permission or scope is not correct in a valid credential. |
Did you enter your credentials correctly? Do you have the required role or permissions for that credential? |
| 404 | Not Found | This error occurs when a URL path does not resolve to an entity. | Did you enter your API URL correctly? |
| 429 | Too Many Requests |
This error occurs when the API server receives too much traffic or if a user’s license or entitlement quota is exceeded. |
The server or user license/quota will eventually recover. The connector will periodically retry the query. If this occurs unexpectedly or too often, work with your API provider to investigate the server limits, user licensing, or quotas. |
For a full list of codes, refer to HTTP response status codes.
Verifying Ingestion
To verify ingestion:
-
Select Threat Hunting.
The Interflow Search tab appears.
-
Change the Indices to Windows Events.
The table immediately updates to show ingested Interflow records.