Introduction to Stellar Cyber
![]() Learn more at Stellar Cyber Academy.
Learn more at Stellar Cyber Academy.
The following links take you to courses on the Stellar Cyber Academy technical training portal where you can learn more about a topic by watching the suggested lessons.
F02 Open XDR Architecture Overview (01h:11m)
Explore key features of the Stellar Cyber Platform, including data processing, storage, and essential functions like Interflow, data normalization, enrichment, and machine learning. Learn how these elements integrate to support efficient threat detection, security operations, and response workflows.
J01 Open XDR: Explained (01h:05m)
Discover how Open XDR integrates security alerts, logs, and telemetry from various sources. Learn about the capabilities of the Stellar Cyber Platform in intrusion detection, threat intelligence, and case management, providing a unified approach to security event analysis.
Explore the value of Stellar Cyber Open XDR for comprehensive visibility across network, endpoint, and cloud environments. Learn how centralized data management and advanced analytics improve threat detection and reduce response times.
Review key features within the Stellar Cyber Platform, including its open integrations with various security tools, vendor-agnostic design, and AI-driven analytics. See how these capabilities enhance security operations and facilitate a cohesive response strategy.
Delve into the critical components that make up Stellar Cyber Open XDR. Understand how integrations with EDR, IAM, cloud security tools, and SIEM functions provide a multi-layered security approach for threat detection and response.
The first time you access a link on the portal during a session, you must log in to access content.
Stellar Cyber Open XDR is a purpose built platform for unified Security Operations (SecOps). Stellar Cyber was designed to deliver the most efficient and easy-to-use approach to defending the entire attack surface. Stellar Cyber takes a platform approach to unifying SecOps, which specifically means building multiple native capabilities into the platform while maintaining an open system such that Stellar Cyber can intelligently command and control (collect and respond) through the rest of the security stack. This allows security teams to get value from Stellar Cyber Open XDR immediately because it works with existing tools and has intelligence (in the form of alerts and auto-correlation) built-in, and to consolidate capabilities where possible based on what Stellar Cyber natively offers. This combination of native and open ultimately drives a more efficient and easy-to-use approach to SecOps while helping SecOps teams remain future-proof as their investments evolve.
-
Native Capabilities: Sensors (includes deep packet inspection, IDS, Malware Sandbox; for NDR), Bi-Directional Integrations, Data Lake/Data Modeling, AI Engine, Threat Intelligence, and Automated Response.
-
Open System: Hundreds of integrations with other tools, products, and data sources, including:
-
All top EDRs supported
-
All top Cloud providers supported
-
All top identity providers supported
-
Top Use Cases
Stellar Cyber Open Extended Detection and Response (XDR) is a modular platform that lets you enable the capabilities that match your operational requirements. You can deploy it as a traditional security operations center (SOC) platform, use it to replace a legacy security information and event management (SIEM) system, deploy it alongside an existing SIEM, or implement it primarily for network detection and response (NDR). Many SecOps teams also deploy the Stellar Cyber Platform more broadly to consolidate detection, investigation, and response workflows within a single system.
SOC Platform
In a SOC platform deployment, you use the Stellar Cyber Platform as your primary detection and response system across network, endpoint, identity, and cloud environments. You deploy sensors, connect available data sources, centralize alerts and telemetry, and manage investigation and response workflows from a single interface. Stellar Cyber functions as both a next-generation security information and event management (SIEM) system and a network detection and response (NDR) solution, correlating multi-domain data and supporting case management, reporting, and automation.
Legacy SIEM Replacement
In this model, you replace an existing security information and event management (SIEM) system with the next-generation SIEM capabilities built into Stellar Cyber. You ingest logs and telemetry into the data lake, configure integrations, enable detections, and manage reporting and threat hunting directly within the platform. Alert correlation, case management, and automation workflows are handled in Stellar Cyber rather than forwarded to another system. This approach centralizes detection and response functions within a single extended detection and response (XDR) environment.
Existing SIEM Complement
If you retain your existing security information and event management (SIEM) system, you can deploy Stellar Cyber alongside it to expand detection and correlation capabilities. In this configuration, Stellar Cyber ingests data, applies multi-domain correlation logic, and generates alerts that can be forwarded to your SIEM so existing workflows remain in place. You continue to use your SIEM for downstream processes while using Stellar Cyber to provide additional detection coverage and investigative context.
NDR
If your primary objective is network detection and response (NDR), you can deploy Stellar Cyber sensors in relevant on-premises and cloud environments and connect selected contextual data sources such as endpoint detection and response (EDR) or identity telemetry. The AI engine analyzes network activity, correlates events across domains, and generates alerts for investigation. You can manage alerts within the platform or forward them to other systems. Over time, you can expand this deployment by adding additional telemetry sources to broaden detection coverage beyond network activity.
High-Level Platform Overview
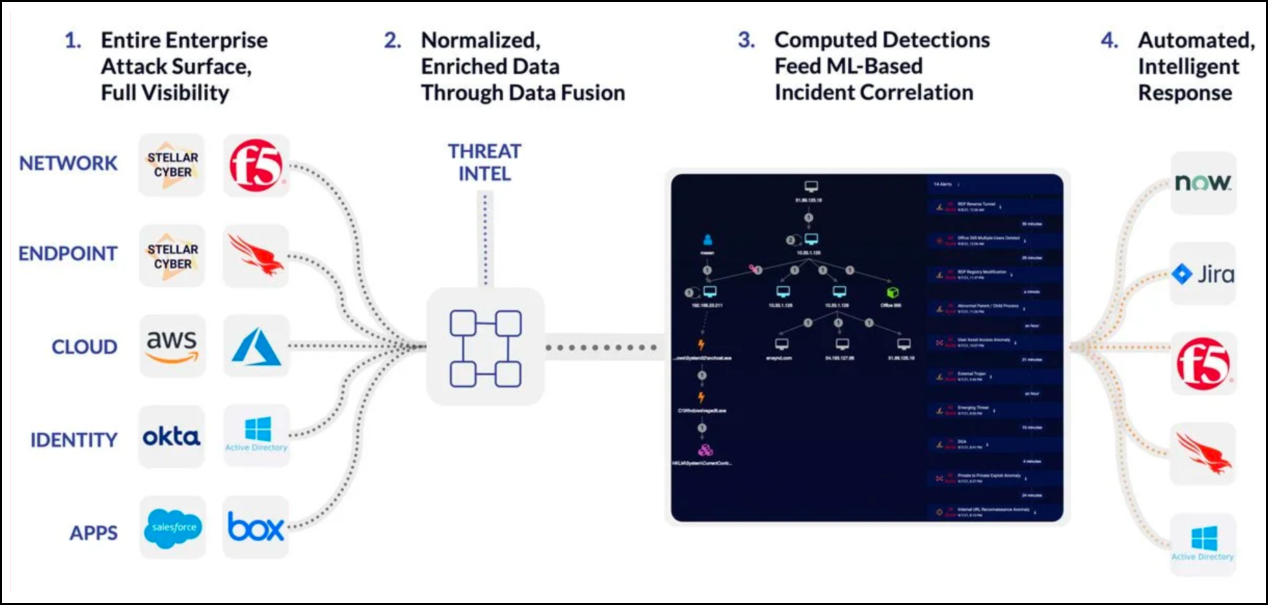
The objective of the Stellar Cyber Platform is to deliver an efficient and easy-to-use approach to defending the entire attack surface. Conceptually, there are four parts to the platform to accomplish that, as illustrated and described below:
1. Collect - Entire Enterprise Attack Surface, Full Visibility
Stellar Cyber Open XDR has hundreds of integrations spanning from API Connectors to Log Source Integrations. Additionally, Stellar Cyber has its own Sensors that package in DPI, IDS, and Malware Sandbox functionality. All three of these sources in conjunction provide visibility over the entire attack surface.
2. Data Processing - Normalized, Enriched Data Through Data Fusion
Regardless of the data source, Stellar Cyber converts all data into the same data model called Interflow. A standard normalized data model is critical for Machine Learning (ML) because source data looks different across environments and vendors and has to be controlled to deploy intelligence reliably. Additionally, Stellar Cyber enriches data with Threat Intelligence and entity information to create valuable records for detection.
3. Detection - Computed Detections Feed ML-Based Case Correlation
Alerts in Stellar Cyber are generated either from Machine Learning or simpler analytic methods (that is, rules). Stellar Cyber creates novel Alerts in its platform based on input data sources and also leverages Alerts from source tools through various Alert Pathways. For example, alerts generated by an EDR can become Alerts in Stellar Cyber after some processing if that EDR is integrated with Stellar Cyber. Stellar Cyber then automatically correlates all Alerts into Cases in real time. A Case represents potentially related activity, either high risk behavior or a real attack.
4. Response - Automated, Intelligent Response
Stellar Cyber users can respond back through a Connector, such as an EDR or Identity provider, in one of two ways. First, mid-investigation, the full response action menu is available so a user does not have to move to another screen. Second, users can leverage automated playbooks to take certain actions based on any criteria to automate as many common workflows as possible.
Refer to Stellar Cyber Architecture for a more detailed overview of the product architecture.
Deployment-Specific Feature Differences
The following table identifies features and capabilities that are available only in SaaS deployments or only in on-premises deployments.
|
Feature or Capability |
SaaS Only |
On-Premises Only |
|---|---|---|
| AI Investigator | ü | — |
| AI-Assisted Case Analysis | ü | — |
| Automatic Triage of Case Alerts | ü | — |
| Automatic Triage of User-Reported Phishing Email | ü | — |
| Air-Gapped Deployment Support | — | ü |
| Direct Backend CLI /OS Access | — | ü |
| Full Data Lake Infrastructure Control | — | ü |
|
Customer-Controlled Upgrade Scheduling |
— |
ü |
| Customer-Managed High-Availability Architecture | — | ü |
|
Customer-Managed Backup and Disaster Recovery |
— |
ü |
SaaS-Exclusive AI Capabilities
The following Al-driven features are available only in SaaS deployments:
-
Al Investigator
Provides Al-generated investigation summaries and contextual analysis.
-
Al-Assisted Case Analysis
Assists analysts by summarizing case activity and highlighting relevant findings.
-
Automatic Triage of Case Alerts
Applies Al-based evaluation to prioritize and reduce manual review effort.
-
Automatic Triage of User-Reported Phishing Email
Automatically evaluates and categorizes user-submitted phishing reports.
These capabilities require a SaaS-based Al infrastructure and are not available in on-premises deployments.
On-Premises Exclusive Capabilities
The following capabilities are available only in on-premises deployments:
-
Support for fully isolated or air-gapped environments.
-
Direct administrative access to backend systems.
-
Full control over Data Lake configuration and storage architecture.
-
Control over upgrade timing and execution.
-
Responsibility for high availability and disaster recovery architecture.