Configuring CrowdStrike (Hosts Only) Connectors (4.3.0 - 4.3.4)
This version of Stellar Cyber's CrowdStrike connector uses API calls to collect Host data and perform response actions (and contain or hide hosts). If you also want to collect Detection Summary Events, you may use the instructions in the topic for CrowdStrike's Falcon SIEM Connector.
Use the table below to determine which configuration options to use for your deployment, based on your Stellar Cyber software version.
|
CrowdStrike Data Type |
Configuration Procedure |
Purpose |
|---|---|---|
|
Hosts |
Stellar Cyber's CrowdStrike (Hosts Only) Connector (this topic) (Uses CrowdStrike's OAuth2 API) |
For v.4.3.0-v4.3.4 Use this to ingest host data and enable manual or automated response actions; records are visible in Stellar Cyber Asset Index. |
|
Incident Detections (Detection Summary Event Logs) |
CrowdStrike's Falcon SIEM Connector (Uses CrowdStrike's streaming API) |
For v.4.3.0-v4.3.4 Use this for mapping CrowdStrike incidents (after deduplication and enrichment) to Stellar Cyber's kill chain and alert index. Records are also visible in the SYSLOG index; |
|
Hosts Detection Summary Events Audit and other events |
Stellar Cyber's CrowdStrike Connector
|
For v.4.3.5 and later Use this connector for ingestion and response actions on a variety of data and map CrowdStrike detection summary events to Alerts. |
This connector uses CrowdStrike's Oauth2 API for collecting host/asset information to handle response actions only.
To add a CrowdStrike connector:
- Generate the CrowdStrike Falcon API key
- Add the connector in Stellar Cyber
- Test the connector
- Verify that assets are received from CrowdStrike
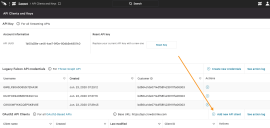
Generating the CrowdStrike Falcon API Key
With streaming APIs enabled, you can generate the CrowdStrike Falcon API key:
Use our example as a guideline, as you might be using a different software version.
-
Log in to CrowdStrike Falcon at https://falcon.crowdstrike.com/ .
-
Click API Clients and Keys.
The API Clients and Keys page appears.
-
Click Add new API client.
The Add new API client window appears.
-
Enter the Client Name.
-
Enable Read and Write for Hosts to contain or hide hosts.
-
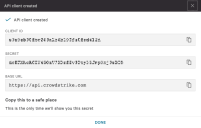
Click Add. The API client created window appears.
-
Copy the Client ID and Secret. You will need these later.
Adding the Connector in Stellar Cyber
With the configuration information handy, you can add the CrowdStrike connector in Stellar Cyber:
-
Log in to Stellar Cyber.
-
Click System | Integration | Connectors. The Connector Overview appears.
-
Click Create. The General tab of the Add Connector screen appears. The information on this tab cannot be changed after you add the connector.
-
Choose Endpoint Security from the Category drop-down.
-
Choose CrowdStrike from the Type drop-down.
-
Choose the Function. If you want to collect logs, click the Collect check-box. If you want to contain or hide hosts, click the Respond check-box.
-
Enter a Name. This field is required, and does not accept multibyte characters.
-
Choose a Tenant Name. The Interflow records created by this connector include this tenant name.
-
Choose the device on which to run the connector.
-
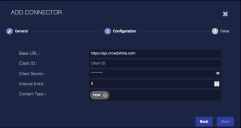
Click Next. The Configuration tab appears.
-
Enter the Base URL. This is the URL of your CrowdStrike portal, and can be:
-
US: api.crowdstrike.com
-
US-GOV-1: api.laggar.gcw.crowdstrike.com
-
EU-1: api.eu-1.crowdstrike.com
-
US-2: api.us-2.crowdstrike.com
For release versions prior to v4.3.4, ensure the URL does not include a trailing "/" symbol.
-
-
Enter the Client ID you copied earlier.
-
Enter the Client Secret you copied earlier.
-
Enter the Interval (min) if you chose Collect. This is how often the logs are collected.
-
Choose the Content Type you would like to collect. The logs for Host are supported.
This connector uses CrowdStrike's Oauth2 API for collecting host/asset information to handle response actions only. Stellar Cyber intentionally disabled the ability to use that API for CrowdStrike incident detections because CrowdStrike's Falcon SIEM connector leverages a streaming API that includes specific content not available in their OAuth2 API.
-
Click Next. The final confirmation tab appears.
-
Click Submit.
To pull data, a connector must be added to a Data Analyzer profile if it is running on the Data Processor.
The new connector is immediately active. You can now contain or hide hosts from the event display, and view or edit those actions on the Endpoint Actions page.
Testing the Connector
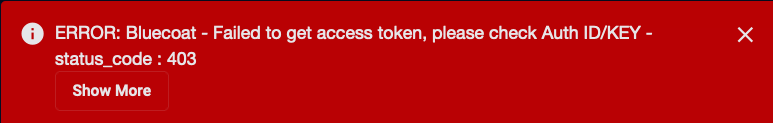
When you add (or edit) a connector, we recommend that you run a test to validate the connectivity parameters you entered. (The test validates only the authentication / connectivity; it does not validate data flow).
For connectors running on a sensor, Stellar Cyber recommends that you allow 30-60 seconds for new or modified configuration details to be propagated to the sensor before performing a test.
-
Click System | Integrations | Connectors. The Connector Overview appears.
-
Locate the connector that you added, or modified, or that you want to test.
-
Click Test at the right side of that row. The test runs immediately.
Note that you may run only one test at a time.
Stellar Cyber conducts a basic connectivity test for the connector and reports a success or failure result. A successful test indicates that you entered all of the connector information correctly.
To aid troubleshooting your connector, the dialog remains open until you explicitly close it by using the X button. If the test fails, you can select the button from the same row to review and correct issues.
The connector status is updated every five (5) minutes. A successful test clears the connector status, but if issues persist, the status reverts to failed after a minute.
Repeat the test as needed.
Verifying Received Assets
To verify Stellar Cyber is receiving assets from CrowdStrike:
- Click Investigate | Asset Analytics.
-
Click the MAC-Identified Assets tab.
-
Enter
crowdstrikein the Search field. The results list is updated.