Configuring CrowdStrike (Hosts/Events) Connectors (v5.0.2+ )
This newer version of Stellar Cyber's CrowdStrike connector integrates CrowdStrike's streaming API to collect detections and events with the existing connector capability that collects host information.
Integration with Crowdstrike enhances Stellar Cyber's threat detection and response capabilities by providing real-time visibility into endpoint security events and enabling automated incident response workflows to contain and mitigate threats. Combining Crowdstrike's endpoint protection with Stellar Cyber's advanced security analytics and machine learning algorithms provides a comprehensive security solution for organizations.
As with earlier versions of the CrowdStrike connector, you can also perform response actions (contain or hide hosts) on the assets that CrowdStrike Falcon manages. Use this topic to understand the configuration requirements and to set the CrowdStrike Connector for deployments running v4.3.5 or later.
If your Stellar Cyber software version is v4.3.0 - v4.3.4, instead use the following topics to configure your CrowdStrike ingestion:
Stellar Cyber connectors with the Collect function (collectors) may skip collecting some data when the ingestion volume is large, which potentially can lead to data loss. This can happen when the processing capacity of the collector is exceeded.
Connector Overview: CrowdStrike
Capabilities
-
Collect: Yes
-
Respond: Yes
-
Native Alerts Mapped: Yes
-
Runs on: DP
-
Interval: Configurable (Applicable only to Hosts)
Collected Data
|
Content Type |
Index |
msg_class |
|---|---|---|
|
Hosts |
Syslog, Assets |
crowdstrike_host |
|
Detection Summary Events |
Syslog, Alerts |
crowdstrike_detection_summary |
|
Events:
|
Syslog |
|
|
Other |
Syslog |
|
Domain
|
<Base URL> where <Base URL> is a variable from the configuration of this connector |
Response Actions
|
Action |
Required Fields |
API |
|---|---|---|
|
dstip, srcip, or |
host ID or device ID and an action which is one of contain, lift_containment, hide_host or unhide_host. |
Third Party Native Alert Integration Details
|
Detections |
For Detections, CrowdStrike's DetectionSummaryEvent and PatternDisposition records are used to derive certain fields for populating the alert into the Stellar Cyber alert index. The Tactic and Technique fields in the record are more directly mapped to Stellar Cyber's XDR Kill Chain. |
|
Hosts |
This content is not applicable for alerts. |
|
Events and other data |
This content is not mapped. |
For details, see Integration of Third Party Native Alerts.
Required Credentials
-
Base URL, Client ID, and Client Secret
-
The API Key must have the following:
-
For Hosts: Enable Read and Write to collect and to contain or hide hosts as a response action.
-
For Audit Events and Detections, enable Read for those as well as Read for Event Streams.
-
Locating Records
Use the following to query for records:
-
msg_origin.vendor:
crowdstrike -
msg_origin.category:
endpoint -
msg_origin.source:
crowdstrike -
msg_class:
crowdstrike_host, crowdstrike_detection_summary, crowdstrike_<event label>orcrowdstrike_<eventtype> (see above content table)
Let us know if you find the above overview useful.
Adding a CrowdStrike Connector
To add a CrowdStrike connector in Stellar Cyber:
- Generate the CrowdStrike Falcon API key you will use in Stellar Cyber
- Add the connector in Stellar Cyber
- Test the connector
- Verify that assets are received from CrowdStrike
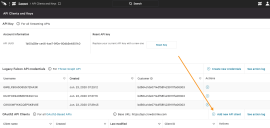
Generating the CrowdStrike Falcon API Key
With streaming APIs enabled, you can generate the CrowdStrike Falcon API key:
Use our example as a guideline, as you might be using a different software version.
-
Log in to CrowdStrike Falcon at https://falcon.crowdstrike.com/.
-
Click API Clients and Keys.
The API Clients and Keys page appears.
-
Click Add new API client.
The Add new API client window appears.
-
Enter the Client Name.
-
Enable Read and Write for Hosts to contain or hide hosts as a response action.
Enable Read for Event Streams and the following content, if you also want to collect the corresponding data: Audit Events and Detections.
Read for Event Streams is required for the content other than Hosts, as of v4.3.5.
-
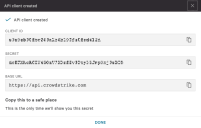
Click Add. The API client created window appears.
-
Copy the Client ID and Secret and note the Base URL. You will need these in the next section.
Adding the Connector in Stellar Cyber
With the configuration information handy, you can add the CrowdStrike connector in Stellar Cyber:
-
Log in to Stellar Cyber.
-
Click System | Integration | Connectors. The Connector Overview appears.
-
Click Create. The General tab of the Add Connector screen appears. The information on this tab cannot be changed after you add the connector.
The asterisk (*) indicates a required field.
-
Choose Endpoint Security from the Category drop-down.
-
Choose CrowdStrike from the Type drop-down.
-
Choose the Function. If you want to collect logs, click the Collect check-box. If you want to contain or hide hosts, click the Respond check-box.
-
Enter a Name.
This field does not accept multibyte characters.
-
Choose a Tenant Name. Use of the connector is restricted to the tenant you select.
-
Choose the device on which to run the connector.
-
(Optional) When the Function is Collect, you can create Log Filters. For information, see Managing Log Filters.

-
Click Next. The Configuration tab appears.
The asterisk (*) indicates a required field.
-
Enter the Base URL. This is the URL of your CrowdStrike portal, and can be:
-
US: api.crowdstrike.com
-
US-2: api.us-2.crowdstrike.com
-
EU-1: api.eu-1.crowdstrike.com
-
US-GOV-1: api.laggar.gcw.crowdstrike.com
For release versions prior to v4.3.4, ensure the URL does not include a trailing "/" symbol.
-
-
Enter the Client ID you copied earlier.
-
Enter the Client Secret you copied earlier.
-
Enter the Interval (min) if you chose Collect. This is how often the logs are collected for Host content.
Interval is applicable only to Host content because the other types are collected with a streaming API.
-
Select the Content Type for which you enabled the API key. You can filter the event types you want to include or exclude, using these content tags
DetectionSummaryEvent (these events are mapped to the Alert Index)
Assorted Audit events:
-
AuthActivityAuditEvent
-
CSPMIOAStreamingEvent*
-
CSPMSearchStreamingEvent*
-
CustomerIOCEvent
-
DetectionSummaryEvent
-
FirewallMatchEvent
-
HashSpreadingEvent
-
Host
-
IdentityProtectionEvent
-
IDPDetectionSummaryEvent
-
IncidentSummaryEvent
-
MobileDetectionSummaryEvent
-
ReconNotificationSummaryEvent
-
RemoteResponseSessionEndEvent
-
RemoteResponseSessionStartEvent
-
ScheduledReportNotificationEvent
-
UserActivityAuditEvent
Other Events: (Use this tag if you want to collect event types not specifically listed above)
You can optionally add the type Other Events to collect any remaining content types.
-
-
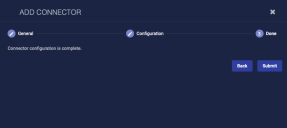
Click Next. The final confirmation tab appears.
-
Click Submit.
To pull data, a connector must be added to a Data Analyzer profile if it is running on the Data Processor.
The new connector is immediately active. You can now contain or hide hosts from the event display, and view or edit those actions on the Endpoint Actions page.
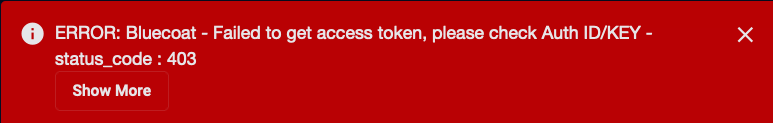
Testing the Connector
When you add (or edit) a connector, we recommend that you run a test to validate the connectivity parameters you entered. (The test validates only the authentication / connectivity; it does not validate data flow).
For connectors running on a sensor, Stellar Cyber recommends that you allow 30-60 seconds for new or modified configuration details to be propagated to the sensor before performing a test.
-
Click System | Integrations | Connectors. The Connector Overview appears.
-
Locate the connector that you added, or modified, or that you want to test.
-
Click Test at the right side of that row. The test runs immediately.
Note that you may run only one test at a time.
Stellar Cyber conducts a basic connectivity test for the connector and reports a success or failure result. A successful test indicates that you entered all of the connector information correctly.
To aid troubleshooting your connector, the dialog remains open until you explicitly close it by using the X button. If the test fails, you can select the button from the same row to review and correct issues.
The connector status is updated every five (5) minutes. A successful test clears the connector status, but if issues persist, the status reverts to failed after a minute.
Repeat the test as needed.
Verifying Content
To verify Stellar Cyber is receiving content from CrowdStrike:
For Hosts:
- Click Investigate | Asset Analytics.
-
Click the MAC-Identified Assets tab.
-
Enter
crowdstrikein the Search field. The results list is updated.
For other content:
-
Click Investigate | Threat Hunting. The Interflow Search tab appears.
-
Change the Indices to Syslog.
-
Search for the desired msg_class as listed in the Collected Data table above.