Key Fields for Alert Types
There are Key Fields for the following:
For information on Key Fields in the user interface, see Key Fields in User Interface.
Key Fields for Third Party Native Alert Types
Stellar Cyber supports third party native alert integration. The Key Fields for third party native alert types are as follows:
|
Third Party Display Name |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
Acronis (Antimalware protection) (acronis_cyber_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Acronis (EDR) (acronis_cyber_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Acronis (Email security) (acronis_cyber_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Acronis (URL filtering) (acronis_cyber_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Avanan (Delivered) (avanan) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Avanan (Quarantined) (avanan) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
AWS GuardDuty (aws_guardduty) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Bitdefender IP (bitdefender_ip) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Bitdefender Threat (bitdefender_threat) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Bitdefender URL (bitdefender_url) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Blackberry CylancePROTECT (cylance_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
CrowdStrike (crowdstrike) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Cybereason (cybereason) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Cynet (cynet) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Deep Instinct (deepinstinct) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Google Workspace Alert (google_workspace_alert) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Huntress (huntress_incident) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
HYAS Protect (hyas_protect_block) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
HYAS Protect (hyas_protect_bad) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
HYAS Protect (hyas_protect_suspicious) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
LimaCharlie Events (limacharlie_alert) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Microsoft Defender for Endpoint (ms_defender_atp) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Microsoft Entra ID (formerly Azure Active Directory) (azure_ad_risk_detection) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Microsoft Defender for Cloud (microsoft_defender_cloud) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Microsoft Defender for Cloud Apps (ms_defender_for_cloud_apps) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Microsoft Office 365 (microsoft_365) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Mimecast Attachment Protect (mimecast_attachment_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Mimecast AV (mimecast_av)
|
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Mimecast Impersonation Protect (mimecast_email_impersonation_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Mimecast Internal Email Protect (mimecast_internal_email_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Mimecast Malicious Receipt Log (mimecast_receipt_with_virus) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Mimecast URL Protect (mimecast_url_protect) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Netskope Alert (Breach) (netskope_protect_breach) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Netskope Alert (Connection) (netskope_protect_connection) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Netskope Alert (Malsite) (netskope_protect_malsite) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Oracle Cloud Infrastructure (OCI) CloudGuard (oci_cloudguard) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
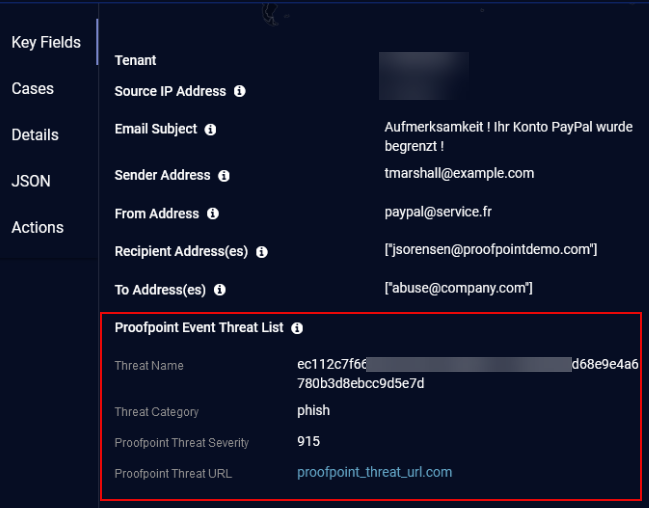
Proofpoint TAP (proofpoint_tap) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
SentinelOne Cloud (sentinelone) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Sophos Alerts (sophos_alerts) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Sophos Events (sophos_events) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Trellix (FireEye) Endpoint Security (AMSI) (fireeye_amsi)
|
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Trellix (FireEye) Endpoint Security (IOC) (fireeye_ioc) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Trellix (FireEye) Endpoint Security (MAL) (fireeye_mal) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Trellix (FireEye) Endpoint Security (PROCGUARD) (fireeye_procguard) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Trend Micro Vision One (trendmicro_visionone) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Varonis DatAdvantage (varonis_datadvantage) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
VMware Carbon Black Cloud (carbonblack) |
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Windows Defender Antivirus (windows_defender_antivirus) |
|
Key Fields for Built-in and Rule-Based Alert Types
The Key Fields for built-in alert types and rule-based alert types are documented in individually. See the Key Fields and Relevant Data Points for any alert type by their display name in Machine Learning Alert Type Details or by their XDR event name in Alert Types by XDR Event Name.
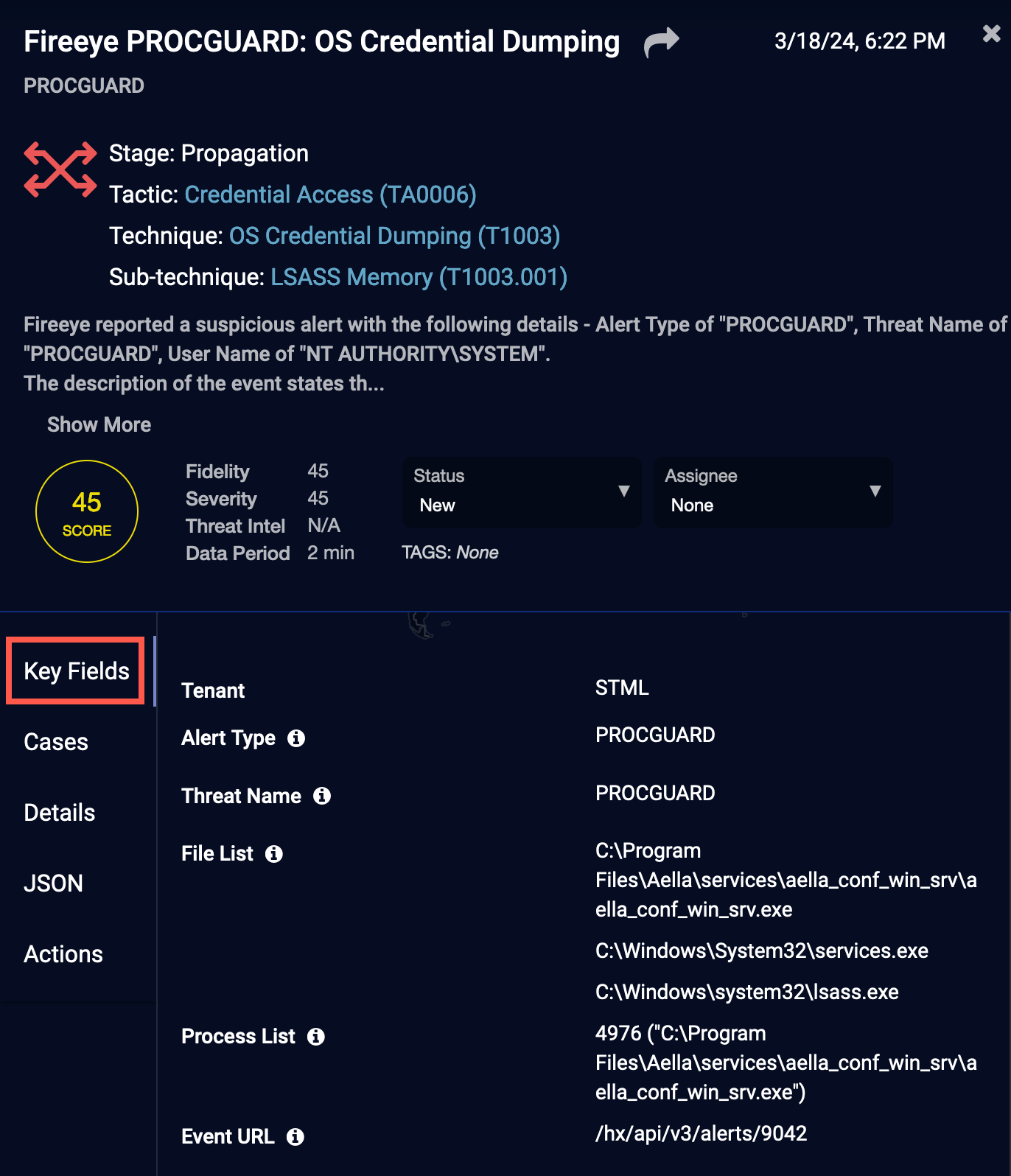
Key Fields in User Interface
To view the Key Fields in the user interface, click the Key Fields tab.
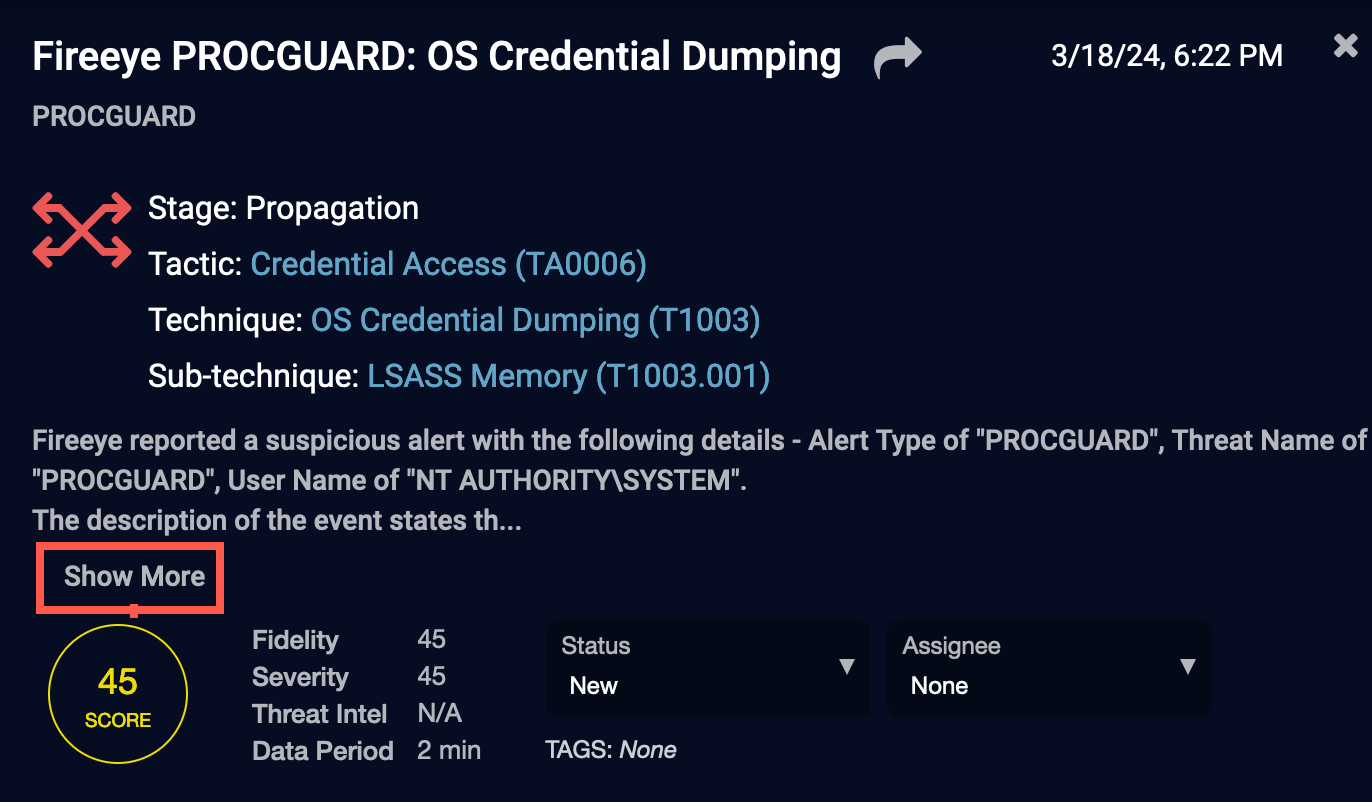
If the alert description is long, click the Show More button to display the full alert description. After the alert description is expanded, the button toggles to Show Less.
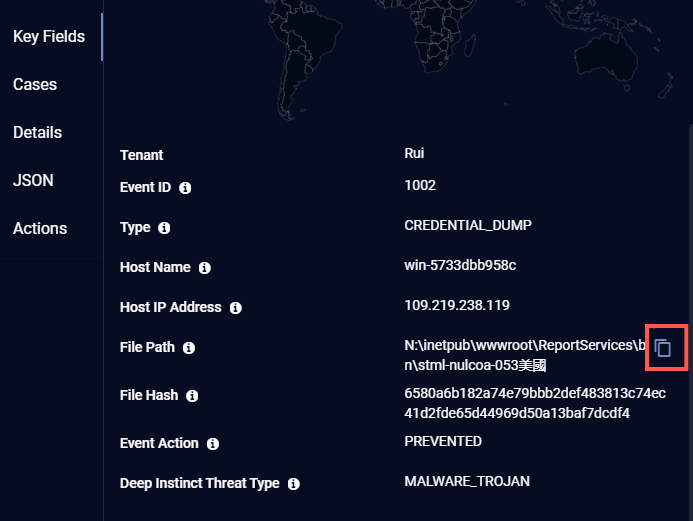
Some Key Fields, such as File Path, have an icon. Click the icon to copy the field value to the clipboard.
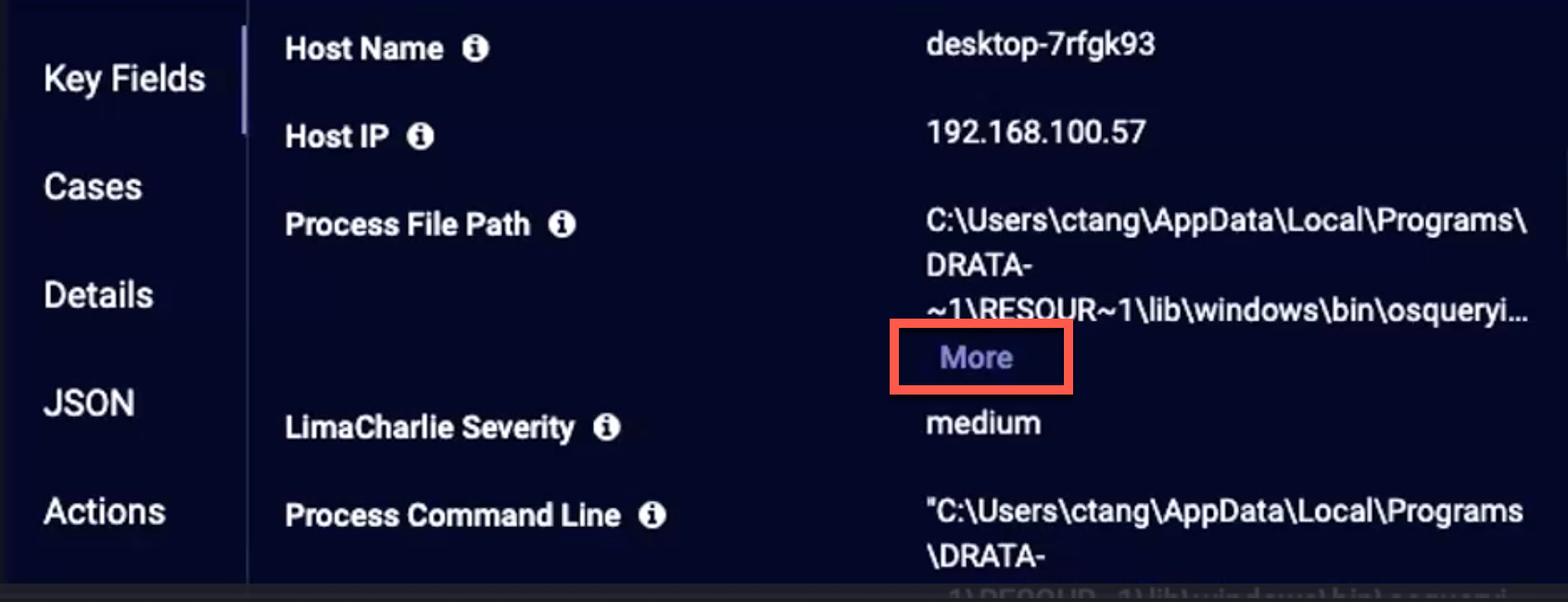
If the value of a Key Field is long, only three lines of text are displayed. Click the More button to expand the value. After the value is expanded, the button toggles to Less.