Installing a Modular, Network, or Security Sensor in Azure
A network sensor monitors the virtual environment, the physical environment if connected to the span port of a physical switch, or the LAN segment via a mirror port on a switch. The sensor monitors network and server response times and can identify applications.
The network sensor converts that information to metadata and forwards it to the DP as Interflow. The DP can then provide security, DDoS, and breach attempt detections.
A security sensor operates as a network sensor and adds:
- sandbox
- anti-virus
- IDS
You can also tunnel traffic over VXLAN from an agent sensor, network sensor, or container sensor to the security sensor so it can inspect those environments.
You can install a network or security sensor on Azure. To install you must:
Preparing
Click to see the minimum system requirements for installing a modular, network or security sensor. Then, select an Azure instance type that meets the stated requirements for your expected sensor workload.
The Azure instance types in the az create commands in the procedure below use the instance types listed below:
Keep in mind that these are example instance types that meet the requirements stated in Virtual Appliance Sizing Specifications. You can select other instance types with the necessary vCPUs and RAM to perform your expected workload, as stated in the system requirements.
- Network Sensor – Standard_B12ms
- Security Sensor – Standard_F16s_v2
- Modular Sensor – Standard_B12ms
To prepare for the installation:
- Open firewall ports for a network sensor or security sensor.
- Open firewall ports for log ingestion.
-
Contact Stellar Cyber support (support@stellarcyber.ai) to have the sensor images deployed in your region. You will need to provide the Azure region for the sensors your are installing.
Do this at least a day before installing, so we have enough time to deploy the images to your region.
Current Azure Sensor Versions
The current sensor versions for Azure deployments are as follows:
- Network Sensor – 4.3.7
- Security Sensor – 4.3.7
- Modular Sensor – 4.3.7
Contact Stellar Cyber support (support@stellarcyber.ai) if you need a different version.
Authorizing the Stellar Cyber Software Images
You must authorize the Stellar Cyber software images so that they are available in the Azure portal:
Use our example as a guideline, as you might be using a different software version.
-
Log in to your Azure portal at https://portal.azure.com/.
-
Click the hamburger menu at the upper left and select the entry for Microsoft Entra ID.
Your Microsoft Entra Overview page appears.
-
Scroll down and click Properties.
The Properties page appears.
-
Copy the value shown for Tenant ID. You need this for the next step and also when creating the VM, so keep it handy.
-
Put your Tenant ID in the following URL and paste it in your browser:
https://login.microsoftonline.com/<tenant id>/oauth2/authorize?client_id=58238038-43b4-4446-8260-0fa97ace1085&response_type=code&redirect_uri=https%3A%2F%2Fwww.microsoft.com%2F
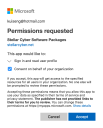
The Permissions requested message appears.
-
Click Consent on behalf of your organization.
-
Click Accept.
-
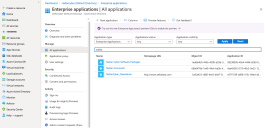
Click Enterprise Applications.
The Enterprise applications | All applications page appears.
-
Search for Stellar. The Stellar Cyber applications that you authorized appear.
If you don't see any Stellar Cyber applications, contact Stellar Cyber support.
-
You can either create a new Resource Group for the deployment or deploy into an existing group. Use this step to create a new Resource Group. Otherwise, you can skip to the next step.
-
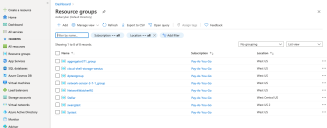
Click Resource Groups.
The Resource groups page appears.
-
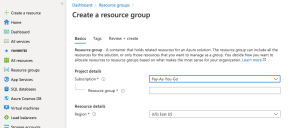
Click Add. The Create a resource group page appears.
-
Choose your Subscription.
-
Enter the name of your group in the Resource group field.
-
Choose the Region where you want to deploy the resource.
-
Click Review create.
-
Click Create. The resource group is created and the Resource groups page appears.
-
-
Click the name of the resource group where you want to deploy the sensor. This is either the resource group you just created or an existing resource group.
The group details appear.
-
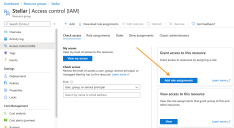
Click Access control (IAM).
The Access control (IAM) page appears.
-
Click Add role assignments to display the Add role assignment controls.
-
Click on Privileged administrator roles and choose the Contributor option, as illustrated below:
-
Leave the default selection of User, group, or service principal in the Assign access to drop-down.
-
Enter Stellar in the Select field. The available Stellar Cyber software packages appear.
-
Choose Stellar Cyber Software Packages.
-
Click Save. The Resource groups page appears again.
-
Click Home. The Azure services page appears.
-
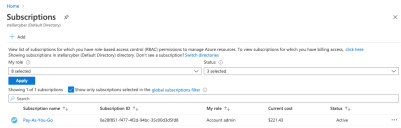
Click Subscriptions. The Subscriptions page appears.
-
Choose your subscription. The subscription details appear.
-
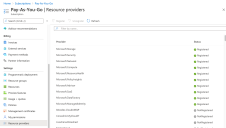
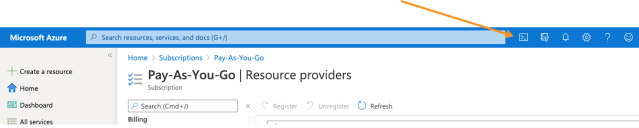
Click Resource providers.
The Resource providers page appears.
-
Select Microsoft.Network.
-
Click Register.
-
Select Microsoft.Compute.
-
Click Register.
-
Click Cloud Shell.
A PowerShell windows opens and connects.
-
Enter the following 3 commands to get an access token from the Stellar Cyber Azure portal:
az account clear
az login --service-principal -u '58238038-43b4-4446-8260-0fa97ace1085' -p '3238Q~KMtVAIyuC6gDVMhboKEW7w6W~bXYQhFcZx' --tenant '2f580e30-1cc1-4c08-9e80-704999508e1a'
az account get-access-token
-
Enter the following commands to get the access token from your tenant ID. Replace Tenant ID with the value you copied earlier.
az login --service-principal -u '58238038-43b4-4446-8260-0fa97ace1085' -p '3238Q~KMtVAIyuC6gDVMhboKEW7w6W~bXYQhFcZx' --tenant '<Tenant ID>'
az account get-access-token
-
If you have multiple Azure subscriptions, use the
az account list --output tablecommand to make sure that the subscription where you want to deploy the sensor is currently the default. For example:CopyPS /home/j> az account list --output table
Name CloudName SubscriptionId State IsDefault
Pay-As-You-Go AzureCloud xxxxxxxx-f477-4f2d-94bc-35c00d3d5fd8 Enabled False
Subscription-Dev AzureCloud xxxxxxxx-ac50-4d82-a6ea-a14db86f3957 Enabled True
Subscription-QA AzureCloud xxxxxxxx-9114-4cb0-a044-7e01f074575c Enabled FalseIn this example, Subscription-Dev has IsDefault set to True and is where the deployment will take place. You can change the default subscription with the
az account set --subscription <subscription>command. Let's change the default subscription to Subscription-QA:CopyPS /home/j> az account set --subscription xxxxxxxx-9114-4cb0-a044-7e01f074575c
PS /home/j> az account list --output table
Name CloudName SubscriptionId State IsDefault
Pay-As-You-Go AzureCloud xxxxxxxx-f477-4f2d-94bc-35c00d3d5fd8 Enabled False
Subscription-Dev AzureCloud xxxxxxxx-ac50-4d82-a6ea-a14db86f3957 Enabled False
Subscription-QA AzureCloud xxxxxxxx-9114-4cb0-a044-7e01f074575c Enabled TrueAfter changing the default subscription, the sensor will now be deployed in Subscription-QA.
-
Create a sensor VM.
These commands all point to the most recent sensor images. You can install different versions by changing the version number in the commands below.
Keep in mind that these commands use example instance types that meet the system requirements. You can specify a different instance type with sufficient vCPUs and RAM to handle your expected workload.
-
Enter the following command to create a network sensor VM. Replace <resource-group> with an existing resource group in your deployment and <version> with the version of software you want to install (for example, 4.3.7:
az vm create --size Standard_B12ms --resource-group <resource-group> --name StellarNetworkSensor --image "/subscriptions/0e28f851-f477-4f2d-94bc-35c00d3d5fd8/resourceGroups/Stellar/providers/Microsoft.Compute/galleries/StellarCyberSoftwares/images/Stellar-NetworkSensor/versions/<version>" --admin-username azureuser --admin-password P@ssw0rd#2022 --os-disk-size-gb 128 -
Enter the following command to create a security sensor VM. Replace <resource-group> with an existing resource group in your deployment and <version> with the version of software you want to install (for example, 4.3.7:
az vm create --size Standard_F16s_v2 --resource-group <resource-group> --name StellarSDS --image "/subscriptions/0e28f851-f477-4f2d-94bc-35c00d3d5fd8/resourceGroups/Stellar/providers/Microsoft.Compute/galleries/StellarCyberSoftwares/images/Stellar-SecuritySensor/versions/<version>" --admin-username azureuser --admin-password P@ssw0rd#2022 --os-disk-size-gb 128 -
Enter the following command to create a modular sensor VM. Replace <resource-group> with an existing resource group in your deployment and <version> with the version of software you want to install (for example, 4.3.7:
az vm create --size Standard_B12ms --resource-group <resource-group> --name StellarModularSensor --image "/subscriptions/0e28f851-f477-4f2d-94bc-35c00d3d5fd8/resourceGroups/Stellar/providers/Microsoft.Compute/galleries/StellarCyberSoftwares/images/Stellar-ModularSensor/versions/<version>" --admin-username azureuser --admin-password P@ssw0rd#2022 --os-disk-size-gb 128
Note that you can optionally specify the virtual network and subnet to be used by each of these VMs as part of the commands that create them by including the
--vnet-nameand--subnetarguments. The networks you specify must exist in the same resource group where you are creating the VM. For example, for a modular sensor:az vm create --size Standard_B12ms --resource-group <resource-group> --name StellarModularSensor --vnet-name <vnet-name> --subnet <subnet-name> --subnet-address-prefix <subnet-cidr> --image "/subscriptions/0e28f851-f477-4f2d-94bc-35c00d3d5fd8/resourceGroups/Stellar/providers/Microsoft.Compute/galleries/StellarCyberSoftwares/images/Stellar-ModularSensor/versions/<version>" --admin-username azureuser --admin-password P@ssw0rd#2022 --os-disk-size-gb 128 -
-
Create inbound security groups for the sensor using the commands below, replacing <resource-group> with the name of your resource group and <NSG NAME> with the name of your network security group
-
Enter the following command for a network sensor. Replace PortRange with the port range you need to the logs you'll ingest.
az network nsg rule create -g <resource-group> --nsg-name <NSG NAME> -n StellarPort1 --direction Inbound --protocol Tcp --destination-port-ranges PortRange --priority 501 -
Enter the following command for a security sensor or modular sensor:
az network nsg rule create -g <resource-group> --nsg-name <NSG NAME> -n StellarPort1 --direction Inbound --protocol Udp --destination-port-ranges 8472 --priority 500
-
Connecting the Sensor to the DP
To connect to the DP:
- Log in to your new sensor. The default username/password is aella/changeme. You are immediately prompted to change the password.
-
Change the password.
After you change the password, your session closes automatically. When you log back in with your new credentials, the prompt changes to DataSensor>.
-
Set the host name. The host name is displayed in Stellar Cyber and should be unique for each sensor:
set hostname <new hostname> -
If necessary, set the proxy HTTP server:
set proxy http://<proxy IP address:port> -
Optionally assign the tenant (if you skip this, the sensor is assigned to Root Tenant):
set tenant_id <Tenant ID from Stellar Cyber> -
Use the
set cmcommand to specify the IP address to reach the management interface of the Data Processor. For a DP cluster, this is the IP address of the DL-master's management interface. For a single DP deployment, this is simply the DP's management IP address. You can specify either an IP address or a hostname. For example:set cm 192.168.44.10or:
set cm example.company.comIf you specify a hostname rather than an IP address, the system attempts to verify the hostname with the DNS server. If the DNS server is not reachable, the system reports the error and lets you either proceed with the configured hostname or quit. This way, you can specify a hostname for the
set cmdestination in an offline environment without access to a DNS server. - Verify with the
show cmcommand. You should see the IP address of the DP listed as the CM Controller and the Status should be Established. -
Use the
show timecommand to view the time zone.During installation, the timezone for sensors are automatically set to UTC+0. Since the logs for some security products may only include the local time without a timezone, Stellar Cyber recommends that you set the sensor timezone to the same timezone as your security product.
-
Log out with the
quitcommand.
The sensor automatically contacts the DP to register itself.
Authorizing the Sensor
You must authorize the sensor when it appears in the network.
You can authorize multiple sensors at a time. So if you're installing multiple sensors, install them all, then authorize them all at once.