Installing a Modular Sensor in AWS
This topic describes how to install a Modular Sensor in an Amazon Web Services (AWS) environment. Refer to the following sections for details:
- About Modular Sensors
- Site Preparation
- Launching the AMI
- Applying a Token to the Installed Sensor
- Configuring a Static IP Address (Optional)
- Terminating an AWS Instance
- Enabling SSSE3 for the Modular Sensor VM
Use our example as a guideline, as you might be using a different software version.
Stellar Cyber does not support the installation of third-party software on its virtual or physical device sensors.
About Modular Sensors
Sensors provide the data gathering foundation for Stellar Cyber's OpenXDR platform, gathering the right data with context. Modular sensors are purpose-built Stellar Cyber sensors that include both the host and the Stellar Cyber monitoring software. They are provided as both physical devices (Photon sensors) and virtual machine images for different target environments.
Previous releases provided a variety of different types of device sensors, including Network, Security, and Modular. Going forward, the only type of device sensor is Modular. You can use the Modular Sensor Profile to enable whatever sensor features you like, creating the same functionality provided by the different sensor types in previous releases.
A modular sensor lets you easily add the features you like to your sensor. This helps simplify your deployment and lets you manage the VM requirements for the sensors based on the modular features they use.
Modular Sensors always include log ingestion. From there, you can enable different features as part of your modular sensor profile:
-
Enable the Network Traffic feature to monitor the virtual environment, the physical environment if connected to the span port of a physical switch, or the LAN segment via a mirror port on a switch. The sensor monitors network and server response times and can identify applications.
The sensor converts that information to metadata and forwards it to the DP as Interflow. The DP can then provide security, DDoS, and breach attempt detections.
-
Enable the Sandbox and IDS features to improve your security posture:
- Sandbox lets you detect malware in files and network traffic through Stellar Cyber's integrated cloud service and also provides anti-virus services.
- IDS lets you detect intrusion attempts using both files and network traffic.
Keep in mind that VM resource requirements increase as you add more features to the Modular Sensor Profile. Refer to Modular Sensor Specifications for details on the resources required to run different combinations of features in a Modular Sensor Profile, as well as how to use the show module and show module request CLI commands to compare provisioned resources against those required to run specific feature combinations. Stellar Cyber only enables a Modular Sensor Profile on a sensor if the host VM's resources can support it.
Site Preparation
Click to see the minimum system requirements for installing a modular sensor.
You must have:
- One IP address with access to a default gateway
- A Stellar Cyber license that can be applied to the sensor
To prepare for the installation:
-
Open firewall ports for log ingestion.
-
Open firewall ports for the features you plan on enabling in the Modular Sensor Profile for this sensor.
- Contact Stellar Cyber support (support@stellarcyber.ai) for access to the AMI. You must provide:
- AWS account name
- AWS account number
- AWS region for the sensor
Launching the AMI
To configure and launch the AMI:
Use our example as a guideline, as you might be using a different software version.
-
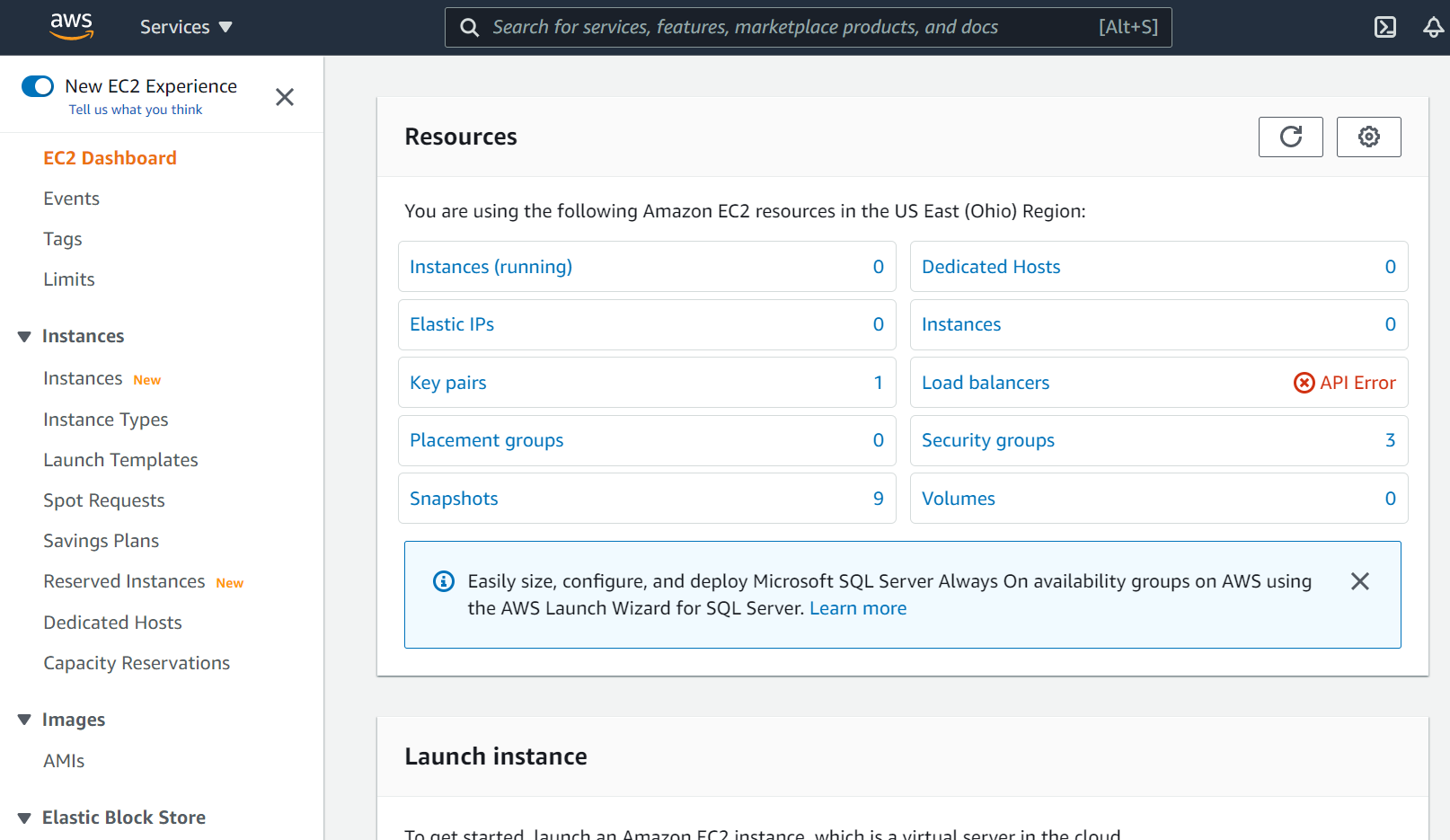
Log in to your EC2 Dashboard.
-
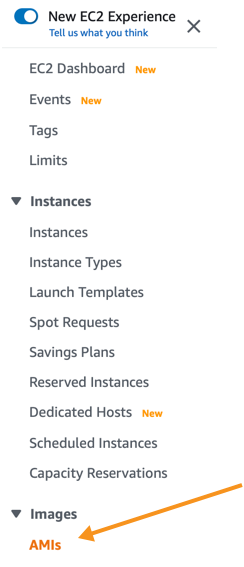
Click on AMIs, under Images.
A list of existing AMIs appears.
-
If you don't see any products, click the drop-down next to the search bar and choose Private images.
If you still don't see any products, make sure your region setting is correct.
And if you still don't see any products, contact technical support.
AMI Names for Stellar Cyber Images
For reference, the AMI names for the Stellar Cyber AMIs are as follows:
-
Modular Sensor – ModularSensor-5-x-y
In all cases, the x-y refers to the minor version numbers of the sensor software (for example, ModularSensor-5-0-3).
-
-
Click the check-box to the left of the AMI. The Launch button activates and the details appear.
-
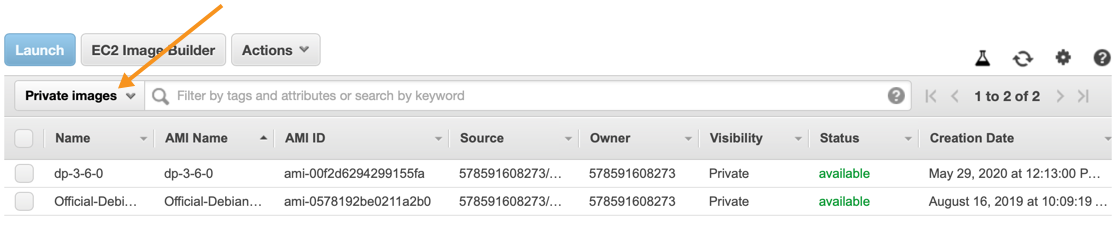
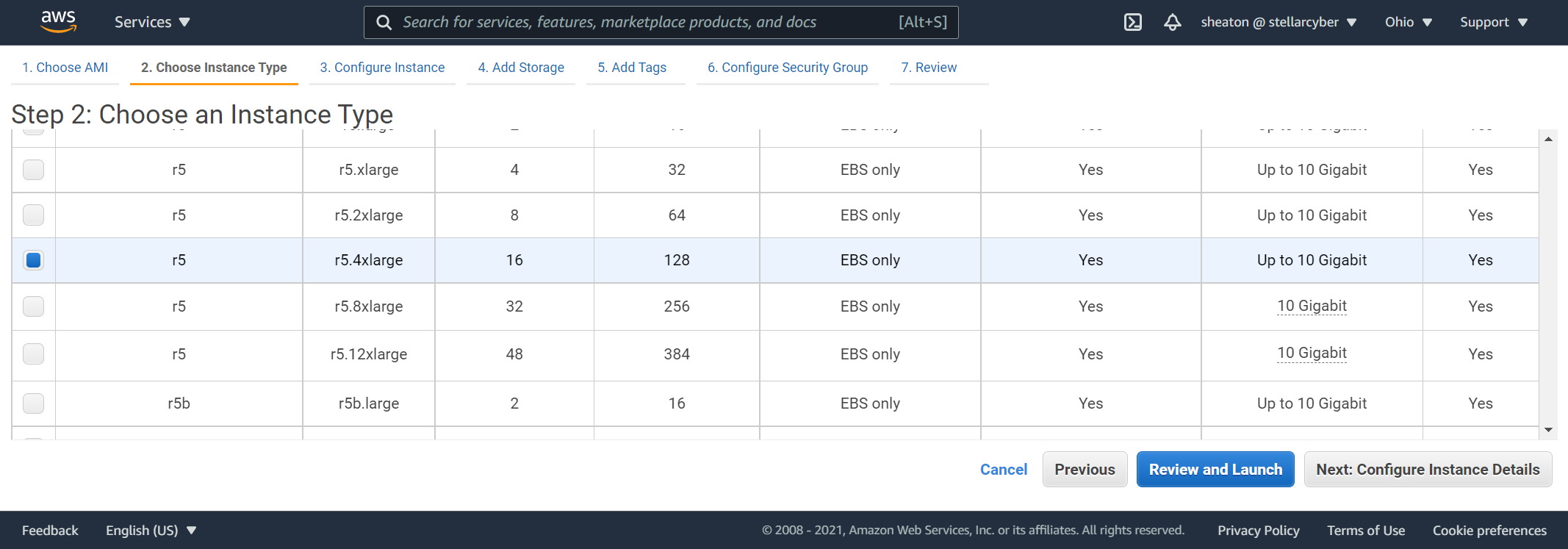
Click Launch. The Choose an Instance Type page appears.
- Choose a t2.2xlarge or higher type. Smaller instance types are not supported.
-
Click Next: Configure Instance Details. The Configure Instance Details page appears.
We recommend keeping the default settings.
-
Click Next: Add Storage. The Add Storage page appears.
We recommend keeping the default settings.
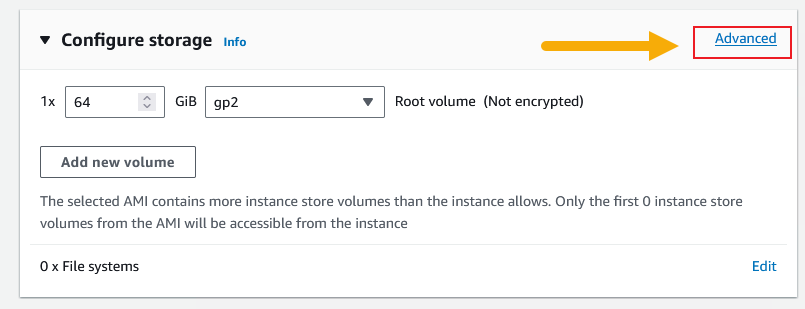
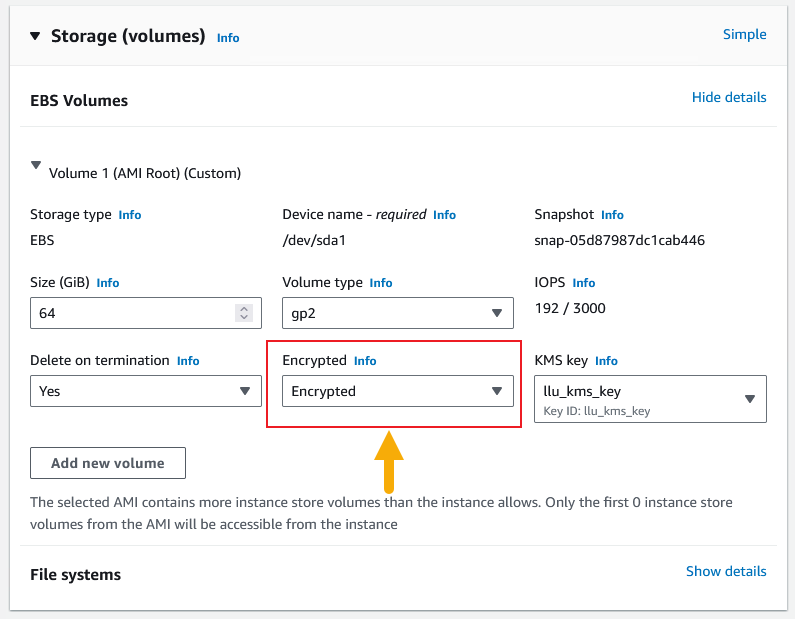
As an option, you can encrypt your storage volume as follows:
-
Click the Advanced button in the Configure Storage panel.
-
Set the Encrypted dropdown in the EBS Volumes settings to Encrypted.
You can also convert an existing sensor's unencrypted storage volume to use encryption.
-
-
Click Next: Add Tags. The Add Tags page appears.
Stellar Cyber does not use tags.
-
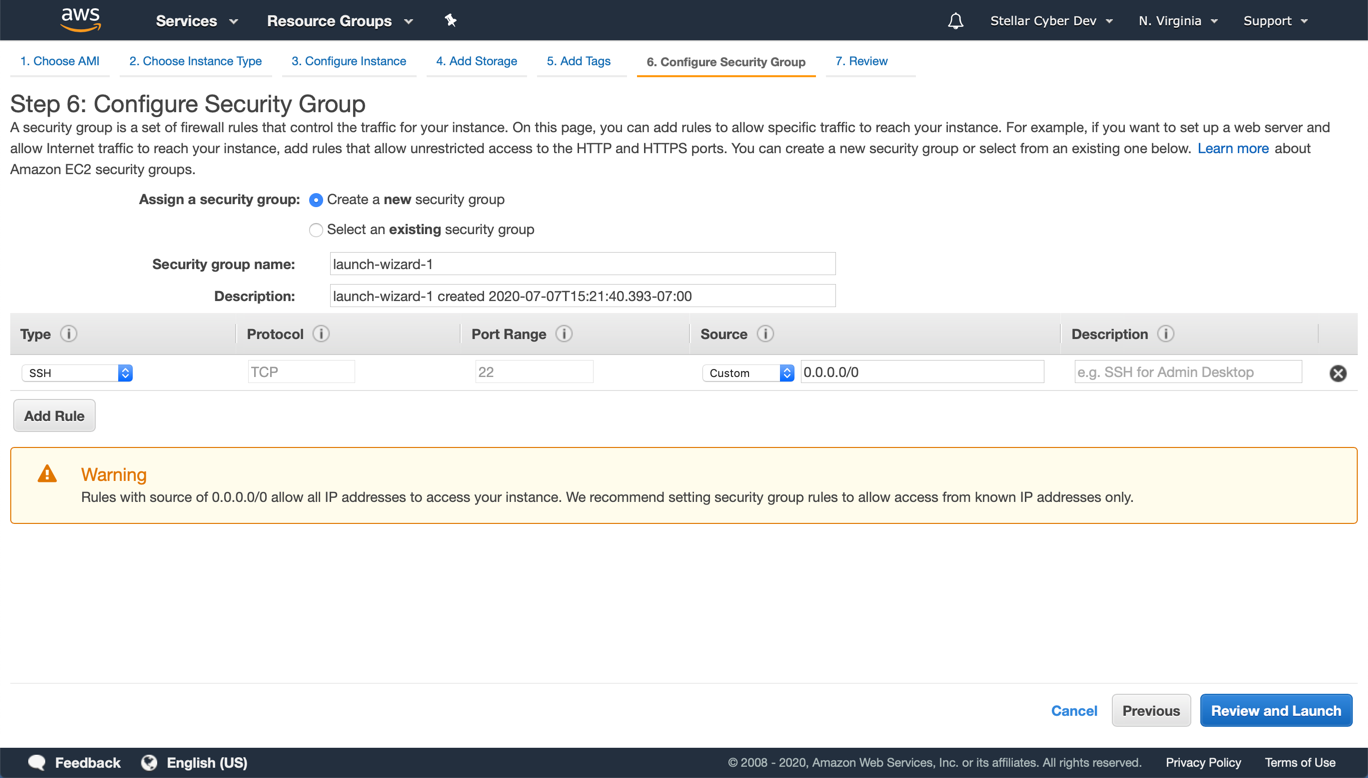
Click Next: Configure Security Group. The Configure Security Group page appears.
You can ignore the warning at the bottom of the page.
Security groups define which local ports and remote hosts can reach the sensor. AWS enables SSH by default.
- Enter the Security group name.
-
Click Add Rule. A new row appears. Configure inbound rules to allow your sensor to communicate with the DP.
If you already added rules on a prior installation, you can choose Select an existing security group to see a list of the existing groups.
-
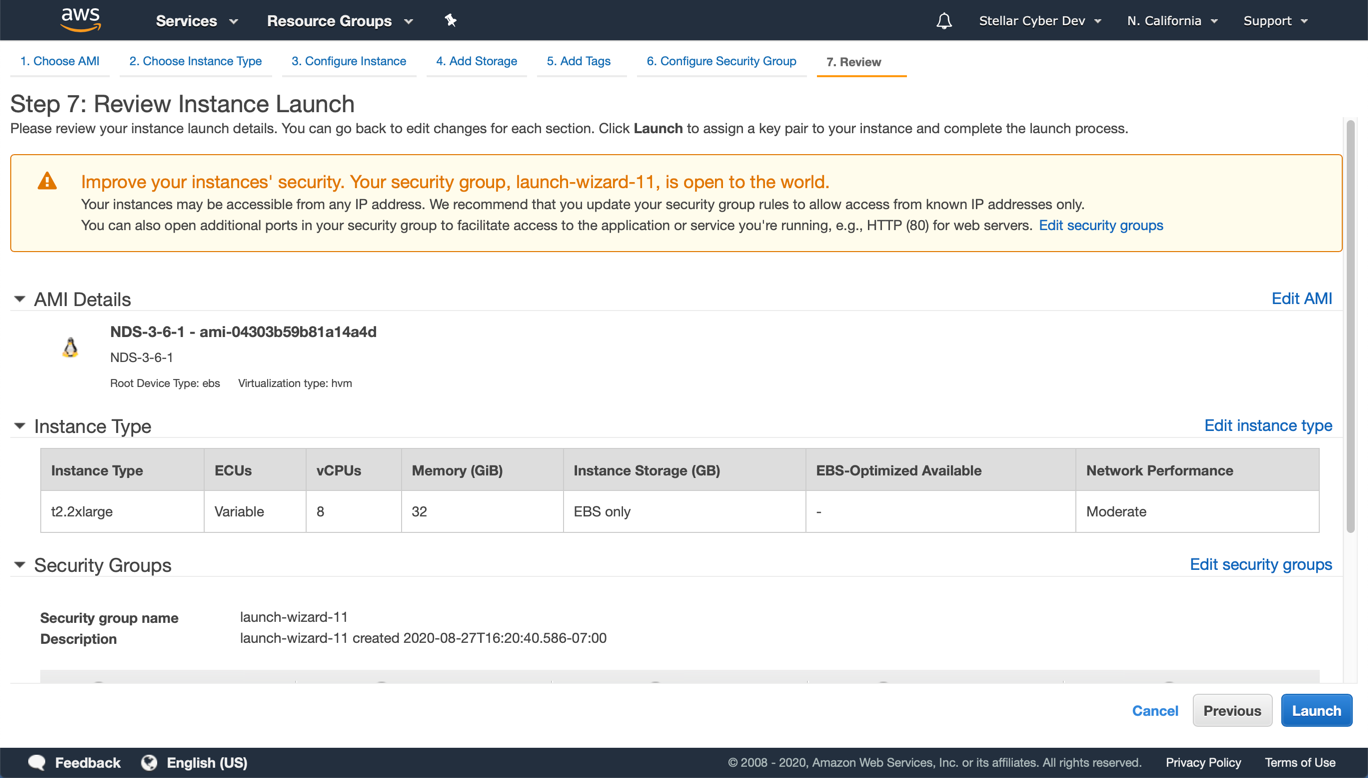
Click Review and Launch. Make changes if necessary.
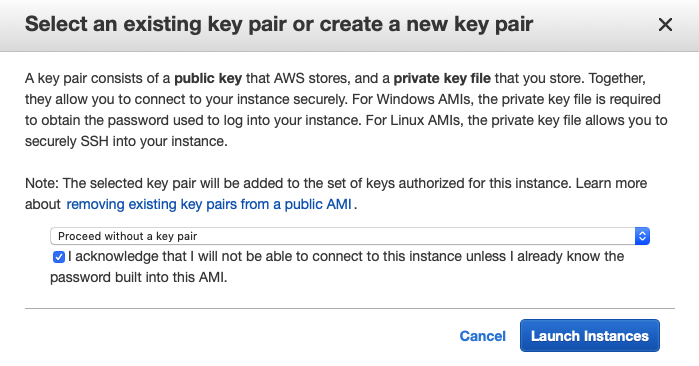
- Click Launch. The Select an existing key pair screen appears. Stellar Cyber is configured with a user name and password, so does not need a key pair.
- Choose Proceed without a key pair.
-
Click the check-box to acknowledge.
-
Click Launch Instance.
You can launch the image but you cannot copy it. This means that the VM must be deployed in the AWS region where the image was authorized.
The VM is now running in the AWS cloud.
Applying a Token to the Installed Sensor
The next step is to obtain and apply the token used to authorize and configure the installed sensor.
Obtaining a Token for the Installation
Tokens are required to authorize and configure the installation of a sensor image downloaded from the DP in the System | Sensor Installation page. Tokens point the installed sensor to the correct DP, assign the specified tenant, optionally provision a selected sensor profile, and authorize the sensor installation.
Use the following procedure to obtain a token in the Tokens tab:
-
Navigate to the System | Sensor Installation page and click on the Tokens tab.
-
If there is already an unexpired token that you want to use for the installation, you can either use the Copy button to copy it to the clipboard or use the Download button to download it as a file.
-
Copy the token if you plan on applying it by pasting it into a
set token string <token>command in the CLI. -
Download the token as a file if you plan on hosting the file on an HTTP server and referring to it in a
set token url <token url>command.
Refer to Assigning Tokens for a summary of the different ways in which tokens can be applied to a sensor installation.
-
-
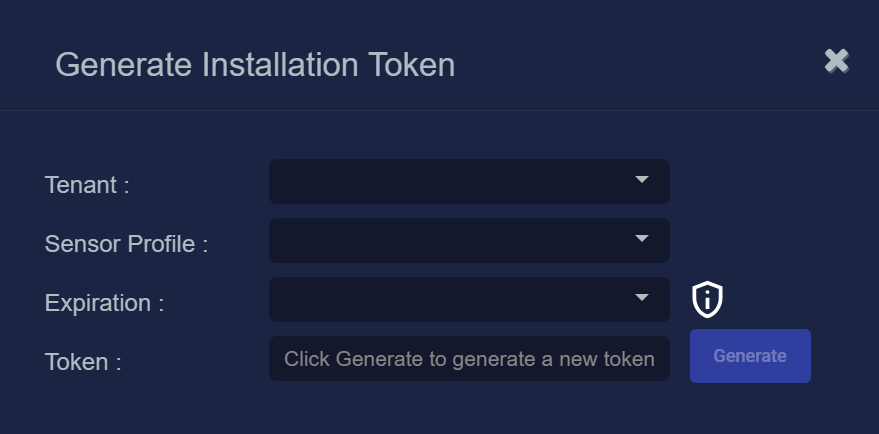
You can also click the Generate button to create a new token.
The Generate Installation Token dialog appears:
-
Select the tenant for the token from the Tenant dropdown. This is the tenant to which all sensors authorized with this token will be automatically assigned. The dropdown lists all tenants configured for your organization in the System | Tenants page.
-
Select the Sensor Profile to be assigned to all sensors authorized with this token from the Sensor Profile dropdown. The dropdown lists all sensor profiles available in the System | Sensor Profiles page for the selected Tenant.
If you do not want to assign a Sensor Profile with a token, you can set this field to None (no sensor profile selected). This is also the setting for any tokens migrated from a pre-5.3.0 release as part of an upgrade.
-
Use the Expiration dropdown to select an expiration date for this token. You can select specified expiration dates ranging from two weeks to three months.
You can also select Never expires for the expiration date. However, Stellar Cyber recommends that you specify expiration dates for your tokens in order to improve the security of your deployment.
Remember that when a token expires, sensors authorized with the token continue to operate as normal. Once a sensor successfully registers with the Stellar Cyber platform, it no longer uses the token. It is only used for the initial authorization, registration, and configuration of the sensor.
-
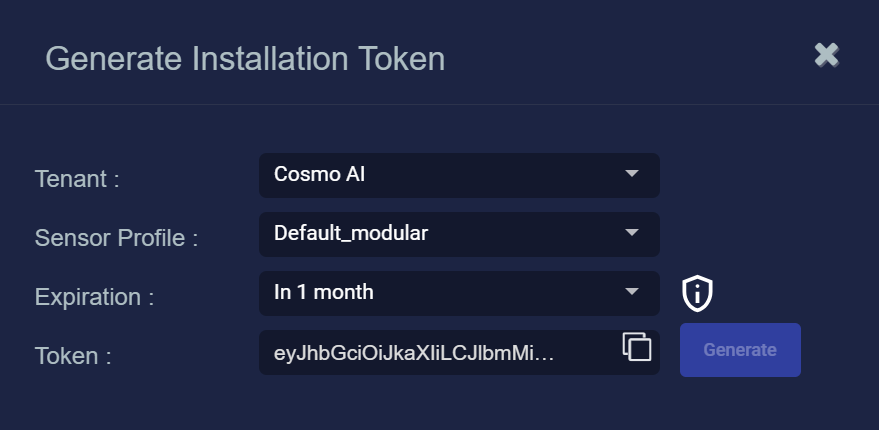
Click the Generate button.
The system generates the token and displays its contents in the Token field. The dialog also updates to display the expiration date for the token, as illustrated below.
-
You can use the Copy button to copy the token to the clipboard immediately, or simply close the dialog and retrieve the token from the Tokens tab later on.
Applying the Token to the Sensor
Tokens are required to complete the installation of a sensor image downloaded from the DP in the Download Image tab.
You apply tokens to sensors as the last step in the overall installation procedure:
- Log in to your new Sensor. The default username/password is aella/changeme. You are immediately prompted to change the password.
-
Apply the token to the installed sensor from the sensor CLI with the
set tokencommand using one of the options in the table below:You only need to use one of the options in the table below. These are just two different ways to do the same thing – apply the token.
Option 1. Copy and Paste the Token String
Copy the token string from the Tokens tab and paste it into the CLI command. The syntax is as follows:
set token string <pasted string>Option 2. Host the Token on an HTTP Server
Download the token as a file from the Tokens tab, upload it to an HTTP server, and reference it in the
set tokencommand. The syntax is as follows:set token url http://<url to token>You can also use an HTTPS server. In that case, the specified URL must also include the username and password for the server using the following syntax:
set token url https://<user:password>@URL> -
The CLI reports that the Sensor token is successfully set.
If you receive an error message instead, it's possible that the token has expired. Refer to the Tokens tab to see the expiration date. If you are using the File technique, it's also possible that an extra space or line may have crept into your text file – check the file to make sure it includes only the token text.
-
Wait a minute or so. Then, verify that the token was successfully applied using any combination of the following techniques:
-
Check the System | Sensors tab in the user interface to see that the sensor has registered itself successfully.
-
Verify that the
show systemcommand shows all services as running. -
Verify that the
show receivercommand displays a receiver. -
Verify that the
show jsoncommand reports some data sent in theBYTE_SENTcolumn.
-
Configuring a Static IP Address (Optional)
By default, the sensor uses DHCP for the management port's IP address. For ease of troubleshooting, however, Stellar Cyber recommends that you reconfigure the management port to use a static IP address. The procedure is as follows:
- Log in to your sensor. The default username/password is aella/changeme, but you changed this when you applied the token in the previous section.
-
You can set IP parameters manually using commands similar to the following (substitute your own IP parameters for the ones shown in bold below):
set interface management ip 192.168.14.100/255.255.255.0
set interface management gateway 192.168.14.1
set interface management dns 8.8.8.8
-
Verify the IP settings with the
show interfacescommand. - Log out with the
quitcommand.
Terminating an AWS Instance
If at some point you decide that you no longer need a particular sensor in AWS, you can always use the AWS documentation to terminate the sensor instance.
Enabling SSSE3 for the Modular Sensor VM
The Modular Sensor VM must have SSSE3 enabled for its processors in order to operate correctly. In most cases, SSSE3 will already be enabled. However, if you encounter issues with packet collection or Interflow data generation, you can use the instructions below to ensure that SSSE3 is enabled.
Sensors installed on Linux hosts must have SSSE3 enabled for their processors in order to operate correctly. This is true for Modular Sensors and Linux Server Sensors, as well as legacy Network and Security Sensors.
SSSE3 is typically supported/enabled for most vCPUs, but may not be for certain legacy AMD vCPUs. See below for instructions on enabling SSSE3.
To enable SSSE3 for a virtual machine:
-
Start the virtual shell (virsh)
-
Type the following command to edit the virtual machine's settings:
edit <virtual_machine_name> -
Locate the <cpu> section. It should appear similar to the following:
Copy<cpu mode='custom' match='exact' check='partial'>
<model fallback='allow'>SandyBridge</model>
......
</cpu> -
Add the following line to the <cpu> section:
<feature policy='require' name='ssse3'/>When you are done, the <cpu> section should appear similar to the following:
Copy<cpu mode='custom' match='exact' check='partial'>
<model fallback='allow'>SandyBridge</model>
<feature policy='require' name='ssse3'/>
...........
</cpu> -
Save changes to the virtual machine and exist virsh.
-
Run the following command:
virsh define /etc/libvirt/qemu/<virtual_machine_name>.xmlEach virtual machine has a configuration .xml file. Typically, these files are stored under /etc/libvirt/qemu, but the location may be different for your system.
-
Stop and start the virtual machine in virsh.